
Of all the malware threats in the world, ransomware remains the number-one choice of cybercriminals. And it’s a growing threat. Cybercrime Magazine estimates that malware attacks will occur at a rate of one every 11 seconds in 2021.
That means there will be 12,000 victims of ransomware attacks by the time you reach the end of this article.
Will your business be one of them? Not if you can help it. And you can – with the right information.
Ransomware is an Ever-Changing, Growing Enemy
According to the U.S. Department of Justice, there are roughly 4,000 ransomware attacks every day in the United States, and the ransoms being demanded by online criminals are growing larger: The largest ransom payout as of August 2021 set a world record at US$4 million.
The rate of growth has been astounding. In 2018, for example, the average ransom demanded payment was US$5,000. In 2020 (just two years later), it was US$200,000 (National Security Institute, 2021).
The target of choice today has also changed.
Previously, the victims of ransomware attacks were mostly individuals. Today, the most popular targets are businesses of all sizes, hospitals, school systems and supply chains. What criminals look for in a victim are organizations that can afford a ransom and that lack sophisticated cybersecurity defenses.
Unfortunately, this new focus means that small to medium businesses are easy targets, because they tend to have more financial resources than individuals, but not enough resources to have robust defenses in place.
What’s the Most Common Ransomware Attack Vector?
When you hear “ransomware,” you probably think of email and social engineering. We usually think about email as a primary delivery vehicle for all forms of malware, and it continues to be an extremely effective way to trick users into deploying ransomware.
But email isn’t the top attack vector for malware. The most popular initial ransomware attack vector is open Remote Desktop Protocol (RDP) systems.
For their 2020 Unit 42 Incident Response and Data Breach Report, PaloAlto Networks studied data from more than 1,000 incidents. They discovered that in 50% of ransomware deployment cases, RDP was the initial attack vector.
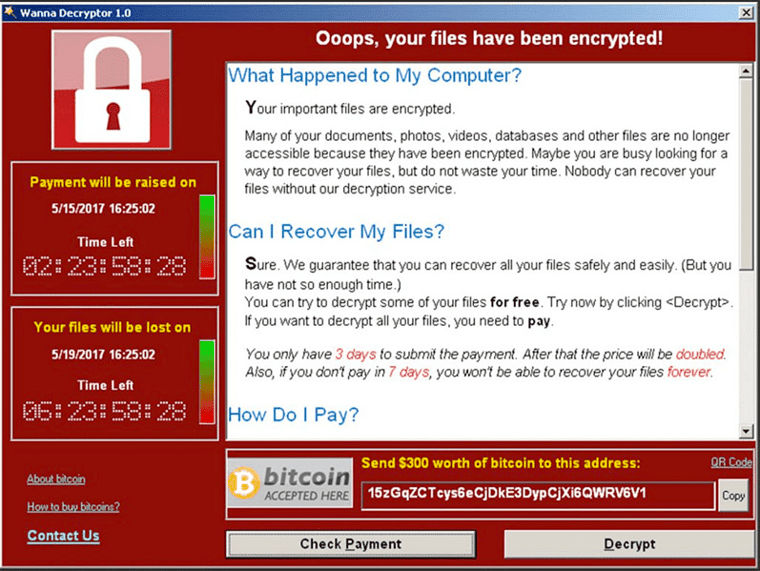
In a typical RDP attack, attackers use brute force to guess username and password combinations on exposed RDP servers until they get onto the server and then drop ransomware. Once the ransomware has a toehold in an organization, it spreads rapidly from computer to computer and server to server by exploiting loose file permissions, open shares and un-patched operating system vulnerabilities.
What to Do if You're Hit with a Ransomware Attack
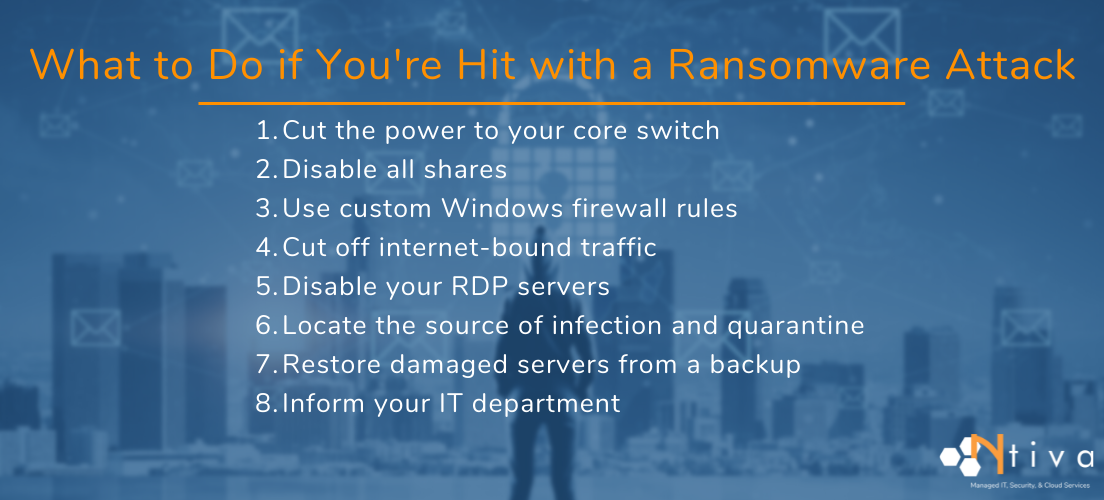
In my role, I act as a virtual CIO for some of Ntiva's clients, primarily focused on cybersecurity challenges. I’ve seen many forms of ransomware, and I'm often asked after an attack, "What should we do first?"
If you’re seeing a ransomware attack happen right in front of your eyes, here's a short list of actions you should take immediately.
1. Cut the power to your core switch
This will stop the ransomware from spreading laterally and keep it from interacting with its control servers on the internet. Don’t do this, of course, if you have applications using your network that protect the health and safety of people. If you have telephones on your data network, they also will stop working.
2. Disable all shares, including admin shares
This likely is going to break some things, but it also will make it harder for the ransomware to spread.
3. Use custom Windows firewall rules
Windows Firewall is your ally here. Use custom Windows Firewall rules to prevent computers from talking to one another over the ports that ransomware is likely to use.
4. Cut off Internet-bound traffic
Cut off Internet-bound traffic at your firewall with a quick rule change.
5. Disable your Remote Desktop Protocol servers
6. Locate the source of infection and quarantine it
Locate the source of the infection and isolate it for later examination. Quarantine all other affected computers until they can be restored.
7. Restore damaged servers from a backup
Restore damaged servers from a backup. (You do have a backup, don’t you? If not, make one today.) But rather than just restoring encrypted files, recover the entire server from a known-good date. Having consistent and well-maintained backups is a key benefit of outsourcing your IT.
8. Inform your IT department or your Managed IT Service Provider of the attack
As soon as you can while taking these steps, tell your IT department or Managed IT Service provider that you have been hacked with ransomware.
Taking these steps will be disruptive. It might even break things. But that’s still infinitely better than ransomware running wild through your organization.
A Few Answers About Paying Ransoms
Q1. Should you pay the ransom?
You will notice that not one of our eight steps to follow during a ransomware attack includes paying the ransom.
This is because enough businesses are paying ransoms that ransomware is now a very profitable enterprise. Cyber insurance firms are making matters worse by telling their clients to pay ransoms since that often is less expensive than recovering systems. All of this, of course, only encourages more criminals.
Q2. Does paying the ransom mean you get your data back?
Does paying the ransom guarantee that the criminals will decrypt your data and give it to you intact? Absolutely not. When you are dealing with criminals, you can’t count on them being honorable.
Need proof? 80% of victims who submitted a ransom payment experienced another attack soon after, and 46% got access to their data but soon learned it was corrupted, according to a survey conducted with 1,263 companies (Cybereason, 2021).
Another thing to remember about ransomware attacks is that the hackers often decrypt the data after a ransom is paid but leave behind a collection of hacker tools to use at a later date.
Variants Of Ransomware You Should Know About
There are a lot of great articles that provide technical deep dives on ransomware variants, but here’s an overview of some of the most important that we're seeing in the field:
Dharma/CrySIS
This originated in 2016 and is being delivered by brute-force attacks on open RDP ports (more on how to protect RDP later). Like other newer ransomware variants, Dharma deletes your local volume shadow copies so you’re not able to recover using earlier saved Windows snapshots.
Emotet, Trickbot and Ryuk
These are three malicious software packages with different functions, and attackers often use them together. Emotet and Trickbot aren’t ransomware, but they’re often used to deploy ransomware, and we’ve seen the used in conjunction with Ryuk. This creates what has been coined “The Unholy Alliance.” They can all be found separately in the wild, of course, but I’m going to lump them together in a single package of woe.
Emotet essentially sets the stage for attacks by gathering information, stealing contacts from Outlook, and generally trying to gain access to whatever data it can. If you see a lot of unexplained locked user accounts on your internal network, it might be a sign Emotet is active. Emotet can update itself several times a day, making it hard for traditional antivirus to find.
Trickbot is sometimes installed by Emotet as a means of capturing keystrokes, stealing credentials, and gathering information from web browsers. Trickbot originally targeted the financial services industry, but we’re starting to see it other places, such as education and the legal sector. It will use encryption to disguise itself from antivirus software. Trickbot, like Emotet, doesn’t encrypt data itself; it lays the groundwork and installs Ryuk.
Ryuk appeared in 2018, a spawn off ransomware that may have been developed by North Korea. Ryuk encrypts data and deletes shadow copies and has earned as much as $3.7 million in ransoms for its operators thus far, according to Crowdstrike. Ryuk was used in the recent Pitney Bowes attack.
How Can You Keep Ransomware from Striking in the First Place?
It’s important to know how to deal quickly and effectively with a ransomware attack, but it’s even better to ransomware from striking in the first place. Is it possible?
With new strains of ransomware appearing in the wild all the time there are no certainties, but you can do a lot to reduce the likelihood of infection and reduce its spread.
Here is a comprehensive list of actions you should follow to help stop ransomware from penetrating your organization:
1. Provide regular phishing prevention training to help your users recognize attacks.
2. Develop a security incident response plan and test it annually. Just like you need to re-certify for CPR, practicing incident response helps your IT team avoid panic and focuses them on their roles in the crisis.
3. Discourage the use of USB drives. You don’t know where that USB drive has been, and neither do your employees. It may be a means of delivering malware.
4. Remove local administrative privileges. You may get some push-back from your employees on this, but it’s a lot harder for ransomware to install itself if the user who triggers it doesn’t have the technical rights to install software.
5. Patch early, patch often. Some ransomware exploits known software vulnerabilities—eliminating those vulnerabilities can prevent its spread.
6. Only publish and connect file shares that are necessary. Since ransomware can spread by file shares and network drives, it’s important to reduce the number of those as much as possible.
7. Follow the principle of least access. People should have access only to the files they absolutely must have to be able to do their work. Ransomware can spread by hijacking the permissions of the person who inadvertently launched it. If that person’s access is limited, so will be the spread of the ransomware.
8. Lock down RDP. Require that anyone connecting to RDP have to verify their identity with multifactor authentication (MFA). Employ an RDP Gateway to isolate the RDP server from direct contact with the internet or place it behind a VPN connection (which requires MFA).
9. Automate intrusion protection. Employ a firewall that will automatically block known bad IP addresses and domains involved in malware delivery. Most firewall web filters should have this capability.
10. Block encrypted attachments at your spam filter. Attackers are encrypting Office files so that antivirus software and spam filters can’t scan them. Blocking encrypted attachments will prevent these from slipping through your defenses.
This may seem like a long list, but think of them as preventative ransomware safeguards.
Reach Out for Cybersecurity Help
Do you find all of this a wee bit overwhelming? We understand. But you need to think of this as a necessary investment in protecting your data from the cyber criminals who essentially running from business to business, trying the locks and windows to see where they can easily break in.
As such, it's no surprise there has been a steep rise in businesses looking for third-party assistance to help them figure out how to lower their risks.
At Ntiva, we’ve helped our clients recover from at least 12 attacks this year alone, and we stop many, many more attacks. If you think you need help with this process, or just want to have your current setup inspected by our security experts, contact us to learn about our Managed cybersecurity Services including a complimentary risk assessment session.
In the meantime, attend our next Cybersecurity Livestream. Join me and your industry peers for biweekly sessions on all things cyber, including breaking news about the latest ransomware threats and valuable lessons and practical advice from the field. Plus, you can get answers to your questions, live.
Back to blog
.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)


