
Law firms come in all shapes and sizes. From corporate to family law, legal practices vary in almost every area, but they all handle confidential client data - and that data must be protected!
Our team of legal IT services experts has put together a list of the four most important tips for law firms, to help ensure the information they manage stays safe throughout the entire litigation process.
1. Monitor for Inbound and Outbound Spam and Phishing
Almost everyone today who uses a computer knows about phishing.
It’s an old trick that many have been a victim of at least a few times.
We all know that we need a solid mail filtering software to prevent everyone in the office from receiving a fresh barrage of malicious attempts every day.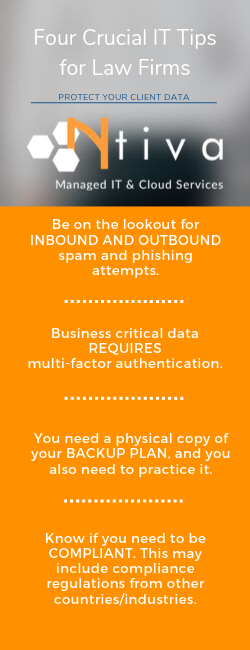
But what about outbound email?
If you think about it, the phishing emails you receive often appear to come from legitimate email addresses from within your company, right?
Law firm domains are especially coveted by cyber-criminals because of their innate clout as a respected domain.
You need to have monitors not only on inbound emails that protect from things like ransomware, but also have outbound monitors as well, so you don’t become propagators of these malicious emails.
Imagine the damage done to your reputation if malicious emails were sent from your domain.
You would have to follow up with everyone who received an email, begging for forgiveness and looking like a fool. You may lose current clients. You may lose future business.
Get ahead of these potential threats and have an outbound mail filter.
While we're talking about email, we need to be realistic and acknowledge that no mail filter is going to stop 100% of the attempts to reach your data.
The only way to prevent from your employees from clicking on links they shouldn't is with continuous end user phishing prevention training.
If your employees don't know what to look for, they will inevitably click a malicious email link, and send your business spiraling into digital chaos.
Proper training programs will send employees randomized tests over an entire year, with fully detailed reports delivered to you, to see who needs more training.
A good mail filter combined with some end user training will help prepare your firm to avoid the worst!
2. Implement Multi-Factor Authentication
Good passwords are hard to remember, so bad, easy-to-guess passwords become the default.
Honestly, no password is strong enough. This is especially true if you’re handling important data.
There’s no way around it. Your on-line business-critical data needs to be protected with multi-factor authentication.
Multi-factor authentication (MFA, also known as two-factor authentication or 2FA) is the process of verifying your identity with a second form of proof. With most forms of MFA, this means entering your password and then inputting a code from your phone.
This second step will keep your account safe from bad passwords, stolen passwords, or even those pesky sticky notes left around the office.
<<WATCH OUR WEBINAR: Password Best Practices for Your Business>>
It's a little known fact, but MFA is the best bang-for-your-buck in technology. There is no better ROI in terms of data security.
For a relatively low monthly cost, your entire office is safe from the usual pitfalls of data protection. If you’re not using MFA yet, you need to make the change as soon as possible.
.png?width=760&name=Law%20Firm%20Quote(1).png)
3. Create A True Business Continuity Plan
Every building has a fire escape plan. And every business needs a full-blown business continuity plan.
Most companies have some sort of back up and disaster recovery solution in place (although make sure you have the RIGHT one in place - some are better than others!)
But you also need to have a fully documented, easily accessible business continuity plan that is shared with everyone who is a part of the plan.
It can't just sit in a drawer (or realistically, on a computer drive somewhere.)
A plan is no good if you don’t know how to implement it or if you can’t access it during a disaster. This means you need to print out physical copies and store them in a safe location AND it needs to be practiced in its entirety once a year.
A serious, well thought out and complete business continuity plan will take real time, effort, and knowledge of your organization’s technological needs and resources.
This can be daunting for a small-to-medium size firm, so consider outsourcing the task to a third party if you can't get it done in-house.
There are plenty of options, such as a Virtual CIO who can step in on a project basis, audit your system and help create a thorough plan tailored to your needs.
Even if it takes some outside help, a business continuity plan can save your business from complete ruin in the case of a disaster.
4. Keep Up With Compliance Regulations
It's surprising how many law firms ,especially the smaller ones, don’t realize they’re breaking the law when ti comes to compliance.
Look at the data you’re handling - is it covered by a compliance regulation? Here are just a few examples;
- If any part of your client data is medical information, you must be HIPAA compliant.
- Do you deal with clients in the UK? They are protected under GDPR
- It's no secret that law firms hold very sensitive client data - all Personally Identifiable Information (PII) must also be protected under both state and federal law
- Complicating matters even more, US states are also passing their own data protection laws
To maintain your reputation as a respected law firm, your clients need to know their data is safe. We recommend starting with this simple quiz from our friends at CRI, "What's Your Cyber Readiness Level?"
If you're unable to keep up with constantly changing standards, it might be time to outsource the task to a Managed Security Services Provider (MSSP) who can protect you on an ongoing basis.
If you'd like more information on how Ntiva can help your law firm, don't hesitate to request a complimentary consultation!
Want to learn more about IT Services and Support for Law Firms? See Ntiva’s Legal IT Services and Support.
Back to blog

.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

