How much should your business spend on cybersecurity? It’s a tough question, and the answer depends on your size, tech stack, industry, and risk tolerance. With so many variables, it’s easy to feel stuck between overspending and under-protecting.
In this post, we’ll break down common cybersecurity tools, what they actually cost, and how businesses of different sizes can build a smarter security strategy that fits their budget.
TL;DR: Cybersecurity spending can feel like a moving target, but a smart plan helps you get the most protection without overspending. This guide breaks down common tools, estimated costs, and how to choose between in-house and outsourced IT models, so you can build a secure, scalable strategy that fits your business in 2025.
Don't want to read the article? Watch the full recording below.
Be sure to register here for the "Cybersecurity for Business Leaders" Lunch & Learn series!
Cybersecurity Challenges for SMBs
Many businesses approach cybersecurity like a small hurdle they have to go over. Some will say, "I have a regulatory compliance standard to meet," or "I realize our cybersecurity is a problem, but it shouldn't be too much to fix." The reality is, that small hurdle is actually a giant wall.
Creating a robust cybersecurity program for a small to medium-sized business requires buy-in from everyone in the company, and the level of success generally comes down to two important resources: cost and time. With these resources in mind, let's take a look at the five most common constraints of SMB cybersecurity.
1. Small operating budgets
Most businesses, unless they're a cybersecurity-focused company, are going to start with a small cybersecurity budget. This means you're going to need to get creative with making that budget stretch.
2. Lack of skilled IT and/or cybersecurity personnel
This comes down to two factors, there is more demand than supply right now for cybersecurity professionals, and the fact that many SMBs in niche markets may find it difficult to hire a generalized IT person to meet their needs. Finding a skilled employee in your specific market can be a huge challenge.
3. A need for numerous part time skills that can't be found in a single full-time employee
This ties in with the last constraint, small budgets and niche markets lead to big trouble when trying to find one person to do the job of what could be five to ten skilled positions. Many of these professionals are masters in one field and are well compensated, so they certainly don't have the motivation to go stretch themselves too thin in a small business setting.
4. Expensive regulatory compliance requirements
For anyone needing to meet regulatory compliance standards, like our Govcon friends currently dealing with CMMC compliance, or those in the healthcare field, you're going to have no choice but to make room in the budget to pay whatever it takes to meet these requirements.
5. Desire for expensive enterprise grade security products
If executives in your SMB come from an enterprise-level business, or keep up with cyber security news, they'll be familiar with larger vendors and cyber solutions. The problem is, those products are tailored to enterprise-level budgets! Most enterprise software isn't offered on a per-license basis. In fact, many base-level subscriptions have a higher annual cost than entire SMB security budgets!
So, what should your business do to navigate these common challenges? Let's take a look at the math behind common cybersecurity products and services to stretch that budget as best we can!
Common Cybersecurity Products and Services: Breaking Down the Math
We know how hard it can be to get the money you really need for cybersecurity projects at the beginning of the fiscal year. Invariably, organizations will put a pause on spending at the beginning of the fiscal year to create a nice padding in the budget for the year.
The best advice I can give for this is to create a list of non-recurring projects and know their costs at the beginning of the year. This way, when those paused funds are released later in the year, you'll be ready and have the projects prioritized.
All this being said, no matter the size of your business, you're going to have some recurring cybersecurity costs. You'll need to plan ahead for these and know that they're a constant hit on your budget.
Here are some of the most common recurring cybersecurity services.
Endpoint Protection and Response (EDR)
EDR is always our first recommendation. At Ntiva, we consider EDR a suite of software that provides anti-virus protection, anti-malware protection, and bonus features like disabling USB support and encrypted data scanners. These are basic features that every company in every industry should have.
Phishing Prevention and Training
90% of successful cyberattacks come from phishing and a lack of vulnerability remediation. Because of this, phishing prevention and vulnerability scanning have become nearly as common as EDR services. The human element is the weakest link, and phishing prevention training will teach your employees exactly what to look for in their day to day work.
The first time we run these phishing prevention training programs, we send a phishing email to your entire organization. I can guarantee you're going to get a report that shows double digit click-through percentage. If your organization of 100 received these emails in real life, 10 of them would put your company at risk.
Over the course of six months, as we continue to test your employees with trickier phishing attempts, we always see the numbers drop. We see most businesses end up with an average 2% click-through rate once training is complete.
Dark Web Monitoring
Dark web monitoring involves our team scouring the dark web for any sensitive information or compromised passwords that can be linked back to your organization. This is completely hands-off from the user end.
Vulnerability Scanning
Vulnerability scanning involves a team constantly performing security testing your network. This process gives you full visibility of any potential problems with data integrity and security. You also need to account for vulnerability remediation. It's one thing to be aware of the problems with your network security, and it's another to fix those problems.
A common myth on the internet is that you can simply skip over any vulnerability scanner and play ignorant when something goes wrong. There have been multiple court cases with organizations of all sizes, and we can almost guarantee that this angle no longer works. You are expected to know any weak points in your data structure, and resolve them before they become an issue.
Multi-Factor Authentication (MFA)
I've lost count of how many times my team has worked on cybersecurity incidents that could've been prevented by multi-factor authentication. It's a simple solution with huge ROI. You simply put in a code from your authenticator app or even an SMS text on your phone along with your normal password. This easy step can literally save your business.
The costs for most of these services are kept at a relatively low (think $5-$10) per user cost. However the exact cost will vary based on things like vendor, package deals, and whether you're going with an outsourced IT firm.
Microsoft Defender
Microsoft Defender for Endpoint is a powerful tool that goes well beyond basic antivirus. It includes features like endpoint detection and response (EDR), attack surface reduction, real-time threat intelligence, and automated investigation and remediation. For businesses already using Microsoft 365, Defender is often already included in the license or available as a cost-effective add-on.
But here’s the catch: most businesses don’t take full advantage of it. Defender is only effective when it’s configured correctly, integrated with other security tools, and actively monitored. That’s where a partner like Ntiva comes in.
We’ve broken down what Defender can do, how it compares to other endpoint solutions, and what to look out for in our full guide: Microsoft Defender for Endpoint: What You Need to Know.
In-House vs. Outsourced IT Services
At Ntiva, we see every kind of IT setup you can imagine. In-house, co-managed IT, fully outsourced, a contracted 9 to 5 IT service provider...but the one constant is that everyone wants to get as much bang out of their IT buck as possible.
In-House
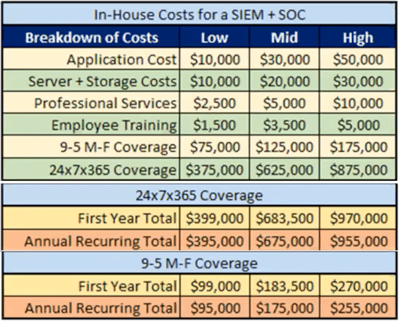
The ballpark numbers you see in this image are based on real-world solutions we have implemented in the past. Low, mid, and high number come in to play based on the size of the business, the location of the business, and how complex the IT environment is.
Application cost is literally the licensing and purchasing required to run the software for your business. This changes based on the software you need and the licensing requirements you have.
Annual server and storage costs includes hardware, subscriptions, and the people required to maintain the technology. Again, this is affected by the size of your organization and the amount of data you're needing to store.
Professional services and employee training involve the upkeep for your tech stack and making sure your employees are up to date as required for any certifications you may have.
There are two types of coverage in this model. Do you want one employee working 9-5 Monday to Friday, or do you need a 24x7 model? The latter model incorporates five people in the line item. Based on the size of your business, this annual number can easily come to $1,000,000.
Outsourced IT
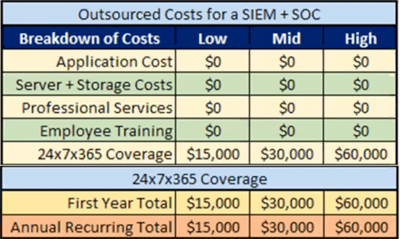
One great feature right off the bat with Ntiva's outsourced IT model is that it's only available in a 24x7 package. You pay a flat rate for coverage every minute of every day of the year.
Another huge benefit is the flat-fee approach. You don't have to account for upticks in professional service costs or application licensing. You pay one flat fee and receive all the IT services you need.
The low, mid, and high costs are meant to cover things like the size and complexity of your organization. A business with 15 laptops and a small centralized web server is not going to pay as much as a 200 person organization with hybrid cloud environments throughout the country.
On average, we find most companies end up somewhere in the low to mid-range per year. This would mean you could receive the same service as in-house managed IT for roughly $370,000 less.
As I said before, these numbers are not made up to scare you. These are real costs I've seen from clients in 2025. Believe it or not, a 24x7 in-house model that is meant to stand up to basic SOC compliance can easily cost $1,000,000 per year.
While there probably will be annual cost adjustments on outsourced IT services, they won't be nearly as great as an in-house setup. For example, you might have to pay $16,000 in year two to cover additional licensing or an extra feature your business needs. But that $1,000 is nothing when compared to annual hardware maintenance and employee compensation increases!
Getting the Most Bang for Your IT Buck
Finding the balance between the IT services you need with the IT services you can afford can be a challenge. The process can be overwhelming on your own, and cutting corners can leave your business susceptible to cyber threats. If you're interested in learning what outsourced IT can do for you business, reach out to our team below!
Back to blog



.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

