
Law firm cybersecurity has never been more important because the stakes are so high and cybercrime is now endemic. For instance, hackers penetrated the defenses of 48 United States law firms in 2016 and used the company merger information they found in their systems to guide insider trading that netted them more than $4 million.
One study estimates that more than 80 of the 100 biggest law firms (by revenue) in the United States have been hacked since 2011.
That’s a startling statistic, but it’s not surprising because any law firm might be routinely entrusted with commercially and financially sensitive client information, including trade secrets and intellectual property.
Sitting on this kind of ‘treasure trove’ is bound to make them attractive to criminals everywhere, and these days everywhere might be no further away than a single phishing email.
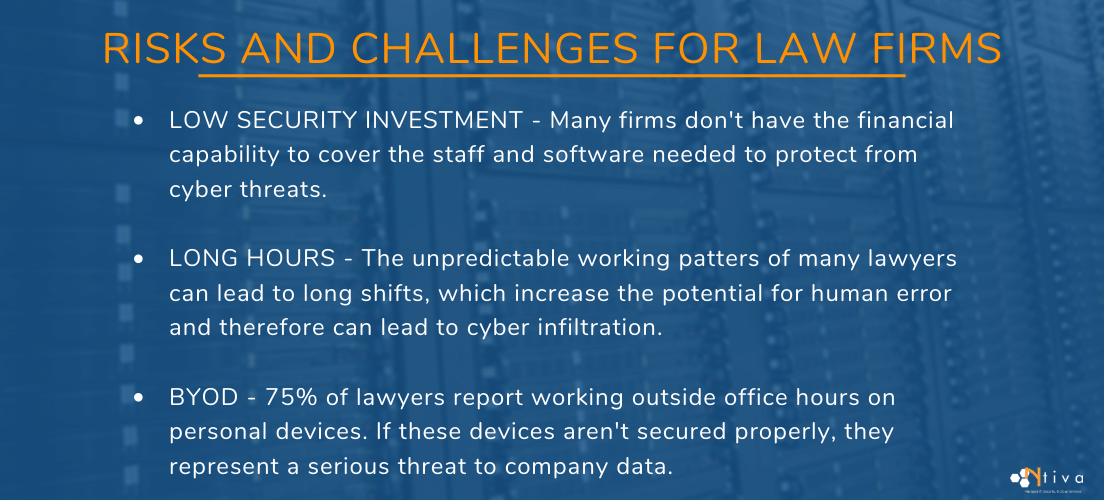
Risks and Challenges for Law Firms
In a busy legal practice, colleagues need and expect access to information on-demand, and to achieve this one might have invested in one or more of the many applications available, like Amicus Attorney, Sage, Timeslips, iManage, LexisNexis, and PCLaw, among many others.
There are so many options out there that it can be hard to choose between them, and just as hard to integrate the ones you do select into a secure and coherent system.
When your law firm needs a system that covers data access, compliance, disaster recovery, scalability, and security, you’ll likely save time and money by talking to a managed IT service provider like Ntiva who can guide you through the most suitable options.
Low Security Investment
Even though cyber threats are increasingly sophisticated and persistent, the way that many legal firms operate doesn’t allow them much financial wiggle room for inward investment in cybersecurity risk management. In fact, even the biggest ones may only employ a handful of permanent staff to focus on it. This is not ideal. But mitigating cybersecurity risk can also result in savings by reducing liability exposure and lowering the cost of Lawyers' Professional Liability insurance.
Long Hours
Another potential weakness in a law firm’s security armor is working patterns. As a business, a firm’s main focus is on billable hours, and lawyers typically work a lot of them. This may be great for their bottom line, but at the end of a very long workday spent grappling with a challenging case, it’s much easier for a tired attorney to drop their guard and accidentally click on an email attachment that infects the system with malware.
BYOD
Leading on from this are the risks associated with remote working (one recent survey found that 75% of lawyers reported working outside of office hours) and BYOD, or “bring your own devices” meaning a personal phone or tablet used for work. A risk management chain is only as strong as its weakest link, and personal devices are not always adequately secured.
A World of Threats
When you put all of these factors together, from a hacker’s perspective some law firms look as tempting as a diamond mine that’s only being guarded by mall cops.
If it seems too expensive to invest in better cybersecurity, it’s definitely too expensive not to. Law firms that fail to adequately defend their clients’ sensitive data against attacks may find themselves in the same unfortunate position as Clark Hill, which is currently embroiled (at the time of writing) in a $50 million lawsuit brought by a former client, Guo Wengui. This Chinese businessman and political dissident had warned the firm that he expected them to be targeted by state-sponsored hackers if they assisted him with his political asylum claim, and his passport details were indeed exposed in online social media later.
Cybercriminals come in all shapes and sizes – from the small fish like bedroom hacktivists to the leviathans around the world like North Korea, China, Russia, and Iran.
When law firms are potentially having to keep sensitive data out of the clutches of bad actors backed by the deep pockets of a hostile state, it’s time to reassess your cybersecurity practices.
Guidance on Data Protection and Regulations for Law Firms
The American Bar Association provides guidance on data security issues facing law firms. Its 2017 survey revealed that 22% of law firms had fallen victim to data breaches and in 2018 that figure rose to 23%, but the true numbers for any year may be a lot higher than what members are reporting because many victims don't even know that their systems have been breached until much later (225 days later, on average, according to one survey).
It also seems likely that many will be wary of harming their reputations by admitting to a data breach, (not to mention being sued by affected clients).
In response, in 2017 the American Bar Association Standing Committee on Ethics and Professional Responsibility put out Formal Opinion 477R, which described the ethical obligations of lawyers to keep confidential client data secure when using the Internet to communicate.
Formal Opinion 483 followed in 2018, stating that “lawyers must employ reasonable efforts to monitor the technology and office resources connected to the internet, external data sources, and external vendors providing services relating to data and the use of data.” It sets out lawyers' data security obligations in detail, along with the crisis management response if a cyber attack or security breach takes place.
Even if this guidance hadn’t appeared, it’s becoming the norm for clients to insist that law firms put policies in place to ensure their information is protected from data breaches.
Standards of Care
Lawyers have long been required to protect their clients’ confidential data, but now the advice is becoming more cybersecurity-specific. ABA Rule 1.1 of the Model Rules of Professional Conduct requires attorneys to “keep abreast of changes in the law and its practice, including the benefits and risks associated with relevant technology.”
The ABA website now includes an article that says law firms must “monitor network activity, review IT reports, and perhaps employ a chief information security officer (CISO) in developing, implementing, and maintaining appropriate cybersecurity programs.” It warns that if they don’t protect against data breaches, they risk becoming the subject of legal malpractice claims, which are on the rise.
Regulations
Law firms are not compelled to meet a set of security standards spelled out specifically for the legal profession by the government regulatory authorities. This compares to state laws referencing PCI DSS for payment processors and the federal statute HIPAA for healthcare.
Still, you’ll have to comply with PCI DSS if your firm handles credit cards, and if a client of yours is subject to HIPAA then you will no doubt handle protected health information and the chain of liability will extend to you. That means that you will need to abide by HIPAA’s strict privacy and data security standards.
It can be tricky to maintain compliance in the face of situations like this and with changing legislation, which is another reason why using a managed IT provider to help you to navigate it makes sense.
Different Types of Cyber Attacks
Here are some typical examples of what a legal team is up against.
Phishing
A phishing attack starts when you receive an email that appears to be from a legitimate source. You open it, click on an attachment and malware infects your device. What it does next can vary greatly, but in one example from 2012, a Toronto law firm lost a six-figure sum in just a couple of weeks when a bookkeeper’s machine was infected with a keylogger that recorded bank account passwords as they were typed in.
Ransomware
Phishing attacks can also introduce ransomware. This software can encrypt all of a law firm’s data, making it unreadable. The only way to restore it is with the decryption key, and the attackers will only give you that if you pay them in bitcoin. Of course, since you’re paying criminals you have no guarantee that they will honor their side of the bargain.
Spyware
Spyware does exactly what you might think, quietly passing on sensitive client information to hackers. Once again it can be introduced via a phishing email, and it could go undetected on your system indefinitely.
MITM (man-in-the-middle)
In this scenario, the attacker acts as a go-between, relaying communications between two parties without their knowledge. The victims think that they’re talking to each other directly, but the attacker is eavesdropping and may also be altering the contents of their messages to gain information that they can exploit for gain.
Cryptojacking
Cryptojacking is an emerging threat. There’s lots of money to be made from mining (manufacturing) cryptocurrencies using computers, but it costs a lot to keep them running. So thieves outsource their expenses by using sneaky software that gets victims’ machines to do the work for them. Compromised machines waste money for the law firm and leave them less able to do the work they were intended for.
What Cybersecurity Steps Should Law Firms Take?
So, a law firm has professional, ethical, financial, and statutory obligations to protect the privacy and security of the sensitive data entrusted to it by clients from the kinds of attacks we’ve listed. And since new risks like the ones we have seen are emerging all the time, law firms need to make sure their approach to risk management evolves to respond.
Change the Culture
The fightback starts with cultural change, and the best way to get the message across is if it comes from the top. Senior partners should signal that cybersecurity is everyone’s ongoing responsibility and that the firm’s viability depends upon everyone’s vigilance. It’s worth investing in training that embeds awareness and then testing its effectiveness with occasional fake phishing emails sent to staff. The idea is that anybody who opens one receives additional training.
Adopt Formal Policies
Only 55% of law firms have formal cybersecurity policies in place, and yet this is the main way of cementing changes in expected behaviors. Policies need to address data protection, training, and how the law firm should respond to a breach.
Appoint Someone to Manage Cybersecurity
If your law firm has the resources, appoint a CISO, or chief information security officer. 67% of law firms hand cybersecurity management responsibilities to IT directors, managers, or non-IT executives, but this isn’t ideal. A cost-effective solution is to outsource a vCISO (virtual CISO) to use as needed.
Backup Procedures
According to the 2018 ABA Legal Technology Survey Report, only 40% of the attorneys that took part said their firms had a disaster recovery plan in place, which makes the other 60% incredibly vulnerable to ransomware attacks. A backup is possibly the best defense against ransomware because you won’t need to pay a ransom for something that you have a copy of.
Update Antivirus Software
Using antivirus software should be a given, but it’s only effective against evolving threats if it’s kept up to date, which should be a standard security procedure.
Regular Software Updates
The Equifax security breach of 2017 (which released personal information that compromised the privacy of 147.9 million Americans) can be traced back to a software patch that the company didn’t install. Updates to operating systems and software often plug security holes, and working with a managed IT service provider is one way to make sure updates get installed as soon as they are released.
Access Restrictions
It’s a good rule of thumb to only let staff access data on a need-to-know basis. Not every staff member needs a key to every door in the building, and this is the same. It’s good practice to compartmentalize system access because this naturally restricts the severity of the damage in the event of a data breach.
File Handling Policy
Flash drives are convenient, but their portability means your data is easier to lose and easier to steal. If anyone at your law firm needs to move files in this way, your policy should insist that drives are encrypted and password protected. An alternative is to use Virtual Desktop Infrastructure (VDI) which avoids the need to store information on devices like laptops. Instead, it’s held on a central server. A managed IT service provider can advise you about this.
Email Security
A law firm’s emails should only be sent using company email accounts. This approach keeps everything in-house where it can be properly protected and audited.
Email use needs to be monitored regularly because employees are only human and they may slip back into using their personal accounts from time to time.
It’s good practice to create a retention policy for email so that only necessary emails are accessible. Again, this is the compartmentalization approach.
It could be quite easy for any firm, large or small, to get bogged down in the details of meeting regulatory requirements from state and national government bodies while providing robust data security. This is one of the reasons why managed IT services from a third-party provider have seen such a lot of uptake in so many industries.
Cybersecurity Risk Assessment
A managed IT provider will conduct a cybersecurity risk assessment that will give your law firm a comprehensive overview of its security posture. This looks at every asset that could be compromised by an attack and the potential consequences that could arise when that happens. The results will help you to prioritize your needs and responses.
Virtual Chief Information Security Officer (vCISO)
If the expense of hiring a CISO seems prohibitive or the size of your firm means that you can't justify a full-time appointment, then the smart alternative is to hire one on an ad hoc basis. A vCISO gives law firms enterprise-level security expertise on tap, aiding compliance but without the hefty price tag.
Multi-Factor Authentication (MFA)
It’s no longer enough just to use a password to secure an account because that only puts one ‘hurdle’ between your data and an attacker. The recommended current best practice for account security is MFA, which you may have come across already. Many apps and services now give you the option of adding a second layer of security, so after you’ve entered the password you then have to enter an authorization code that’s sent to your phone via SMS text, for instance. This additional step makes it much harder for a hacker to penetrate a law firm’s defenses.
Intrusion Detection and Response (IDR)
IDR has an automated threat detection system that monitors your law firm’s network around the clock. It’s even sensitive to the tell-tale signs of potential intrusions. Any red flags (like sudden changes in a user’s activity) are passed on to security experts who can review them and respond to threats in real time, which means your business can continue without interruption.
Endpoint Detection and Response (EDR)
Anti-virus software and firewalls are some of the basic building blocks of your cybersecurity infrastructure, but they only amount to the bare minimum of what you’ll need to protect against a data breach. You’ll want something more intelligent in place to protect your law firm from today’s increasingly sophisticated hacking attempts, which is why EDR was created.
EDR is powered by AI that is smart enough to respond to attacks even when the firm’s devices are operating beyond its firewall. On top of that, a 24-hour Security Operations Center (SOC) provides additional analysis of potential threats. Again, this is the kind of service that you can buy on-demand, so it needn’t be prohibitively expensive.
Phishing Prevention Training
More than 90% of law firm security incidents start with a phishing attack that targets employees because hackers see people as a point of weakness. They're a risk management priority, and a managed IT provider like Ntiva can keep your law firm staff engaged with anti-phishing training including monthly simulated attacks and targeted educational material when an error is made. This automated approach increases staff's ability to respond effectively to phishing attacks.
Vulnerability Scanning and Remediation
A vulnerability scanning and remediation tool actively scans networks for missing security patches, unsafe settings, and services that aren’t needed. The tool then analyses, prioritizes, and addresses vulnerabilities, fixing them before they can be exploited by attackers.
Cybersecurity is now too important to leave to chance, and that’s where Ntiva comes in. We can help you develop the right strategic technology plan so that your law firm meets the security, efficiency, and compliance demands that face it now and in the future.
Want to learn more about IT Services and Support for Law Firms? See Ntiva’s Legal IT Services and Support.
Back to blog

.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

