
For a very long time, conventional wisdom has held that Macs are much less vulnerable to cyberattacks than PCs.
This is no longer the case, and many organizations that thought they were safe are now feeling the pain — and dealing with the aftermath.
Given the nature of modern cyberattacks, it’s more important than ever to understand current cybersecurity standards for your corporate Apple environment. Here’s our guide to what those standards are and how they apply to your business.
Don't want to read the article? Watch the full recording below.
Be sure to register here for the "Ntiva Live: Apple for Business" webinar series!
Macs Need Security, Too!
Believe it or not, new security threats against Macs are outpacing Windows by a two-to-one margin.
There’s no quick fix when it comes to Mac cybersecurity. Instead, it’s best to take a holistic approach that combines physical, administrative, and technical controls in a system of layered security.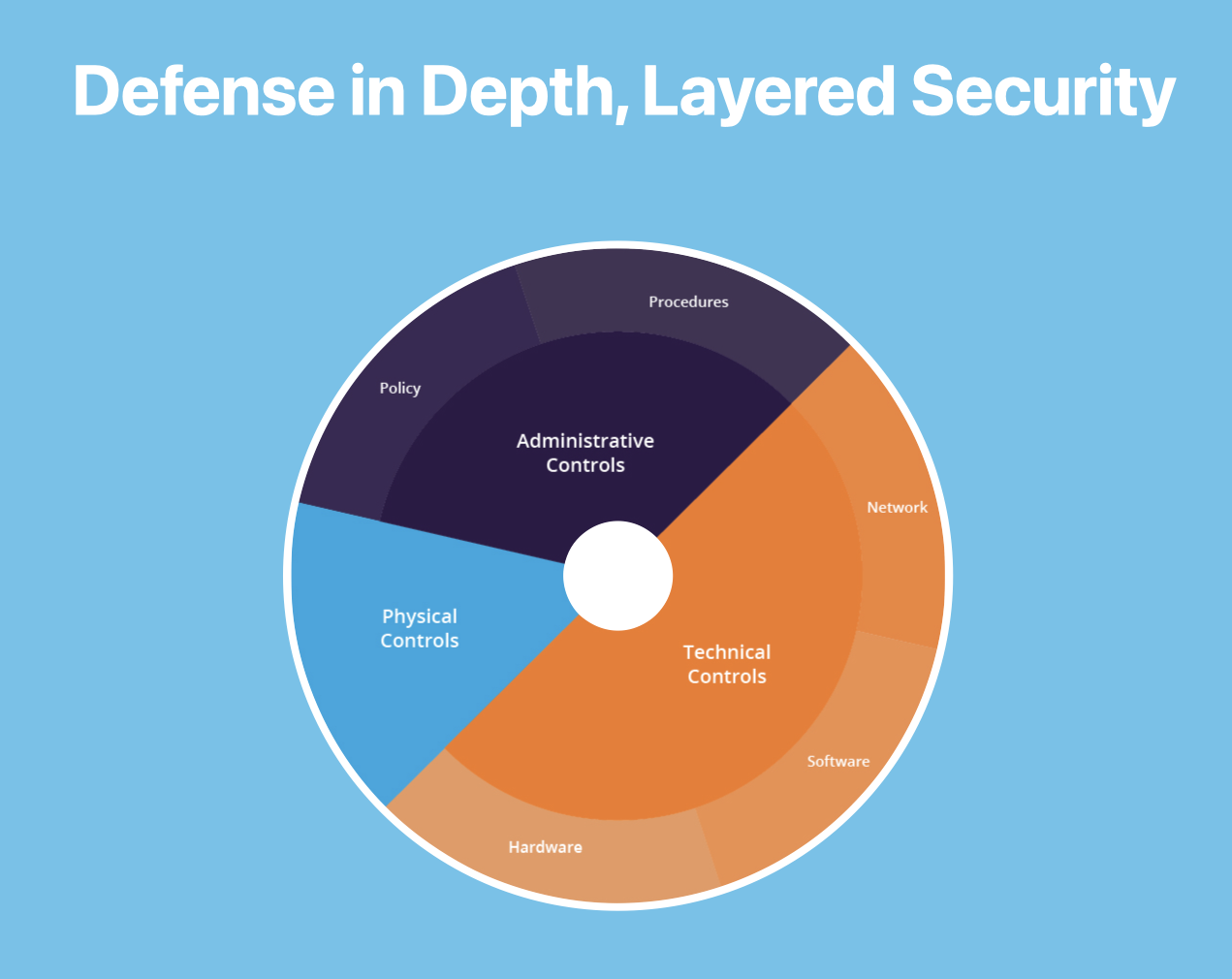
The security standards we’re looking at today are a combination of technical controls for hardware and software — two big pieces of the security pie. Everything we mention in this article can be automated with our Apple Toolkit solution. Let’s dig in.
The Mac Security Standards to Know:
Display Auto-Lock
When you leave your phone on a table, does it sit unlocked until you return? Probably not. Most people’s phones are set to automatically lock after sitting idle for a certain amount of time. Similarly, it’s recommended that you enable the display auto-lock settings for your company’s Macs as one way to keep your information safe.
Note: The screen lock is actually considered a function of the screensaver. With these settings enabled, once the screensaver kicks on, it will require a password to regain access to the computer. That way, if you’re working on a company machine from your local coffee shop or some other public location where you may step away, even if the computer is physically compromised, the contents cannot be accessed.
Endpoint Protection
Endpoint protection is the modern-day equivalent of running an antivirus solution on your computer. It’s a type of protection that Mac users have long ignored, based on the inaccurate assumption that viruses were only a concern if you worked on a Windows PC.
Today, however, we routinely see Macs that have been compromised, due at least in part to lacking endpoint protection. At Ntiva, we primarily work with solutions like SentinelOne and Malwarebytes, both of which provide great results.
FileVault Encryption
If you have a notebook and an SSD, we strongly encourage you to enable FileVault encryption on your machines. It’s a powerful security measure that, once enabled, requires a unique passcode to decrypt the information on your hard drive.
As with many of Apple’s security measures, FileVault requires you to opt-in before it will function, which means setting all your machines to have this tool running. It might feel like you’re asking a lot of your users, but tools like FileVault play an important role in safeguarding your machines. At Ntiva we help our clients automate this process and prepare their team for Filevault encryption.
Firewall
If you’re a long-time Mac user, you may already be familiar with Apple’s software firewall. It isn’t a new feature, but for a long time it’s been notoriously bad, to the point of being almost unusable.
Although this reputation persists, it’s no longer warranted — Apple has stepped up its game and we now recommend making Apple’s firewall a part of your security protocols.
But bear in mind that this is only a software firewall. It won’t protect your network. It’s designed to control incoming and outgoing traffic for specific apps and processes on your computer.
Fortunately, the default settings Apple provides are very agreeable and still allow the user to explicitly add or deny certain kinds of traffic. Enabling this for your organization will likely add a pretty small footprint while offering real security benefits.
Gatekeeper
Gatekeeper is a security feature that prohibits apps from launching if they’re not signed in as authorized. In general, this is a solid practice to prevent bad actors from launching their own apps from your machine or to stop users from downloading and launching apps that may not be safe.
There may occasionally be reasons for a user to override Gatekeeper, but they tend to be very specific to the needs of the individual organization. So, while we generally recommend the standard Gatekeeper policy with overrides disallowed, we can help you make sure the devices in your fleet that truly require access to unsigned applications are also able to launch them.
Login Window
These days, it’s a poor practice to set your machines to automatically log in on boot up. Whatever convenience it may offer is grossly offset by the security risk. Instead, we recommend changing your settings so automatic login is off, and usernames and password hints are not displayed.
As with some of the other security measures we’ve outlined here, this is not the default setting on Macs. It is, however, a simple precaution that can help protect your machines from unauthorized access.
Passcode Policy
One of the simplest steps you can take for Mac security is to implement a passcode policy. The goal is to ensure your team uses strong passwords that won’t be easily guessed (as opposed to something like “Password123”). Setting some basic passcode standards can go a long way toward protecting your machines. Note that if you use our preferred method of authorizing your Macs to look to Microsoft or Google for authentication, your passcode policy will come from your identity provider.
And while we’re on the subject, there is one myth we’d like to dispel — there’s really no advantage to enforced password expiration. If your industry requires expiration as a security standard, that’s okay. But in general, we’d recommend requiring complex passwords rather than implementing a policy that forces change after an arbitrary number of days. Those forced changes aren’t just frustrating for users; they’re also bad practice.
Remote Login and Remote Management
Sometimes your users are going to need help with their Macs. When that happens, and they reach out to an IT support team like Ntiva, Mac’s built-in remote login and management settings allow us to automatically open the doors that we need to provide them with support.
This gives us the ability to assist your users directly, then securely “close the door” behind us when the problem is resolved. This helps ensure bad actors can’t use those same avenues to mount an attack, but without affecting the ability of remote staff to access what they need.
Be Intentional About Mac Security
While the above represent today’s macOS security standards, these standards are always evolving. Rather than taking a “set it and forget it” approach, it’s important to continually evaluate your operations against the most current recommended practices.
Of equal importance is the human element in all of this. Your users should know and understand the security measures you’re putting in place and why you’re enabling them. Good communication is a key part of getting users to buy in and support what you’re doing. That way, instead of being frustrated by the unexpected change — and any extra work involved — they’re on board with being your partner in cybersecurity.
Though new cyber threats will always arise, being intentional about your approach to Mac security can help keep your organization safe. And if you ever need extra support, we’re always here to help.
Back to blog

.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

