
Managing your users and devices can sometimes feel like a pain. If your systems require that every new device is manually configured for every new user, it can add a lot of tedious work for your IT department. If those devices also use complex authentication processes that require multiple passwords, your users may feel frustrated each time they log in to their machines.
To alleviate these pain points, Ntiva uses a tool called Addigy Identity that allows users to log into their Macs using the same login credentials and two-factor authentication they already use for their email accounts. This solution works whether your email is hosted by Google or Microsoft 365, reducing friction for your users without sacrificing security.
Addigy Identity takes advantage of changes Apple made to its support for single sign-on in 2019. This integration pays off for your organization by providing a streamlined authentication process and zero-touch deployment for your users.
Let’s take a closer look at what Addigy Identity does and how to configure it for your organization.
Don't want to read the article? Watch the full recording below.
Be sure to register here for the "Ntiva Live: Apple for Business" webinar series!
What Is Addigy Identity?
Addigy Identity is an add-on to Addigy, the mobile device management (MDM) software we use to manage and secure Apple devices for your workplace. With Addigy Identity, anyone on your team can unbox a new Mac and use their company email address and password — even two-factor — to create their Mac account.
In addition, suppose you have dozens (or even hundreds) of Macs already deployed. By enabling Addigy Identity, existing Mac users will be prompted to enter their company email address, password, and two-factor. (You are enforcing 2FA/MFA on all accounts, correct?) Addigy Identity will sync the local Mac account with the matching cloud account. And if a team member needs to change their password using Microsoft, Google, or Okta. In that case, Addigy Identity will update the local Mac password to match — always keeping the local Mac password synced up with the password set with your identity provider.
Setting Up Addigy Identity
As you set up Addigy Identity to authenticate your users, you’ll have several options for configuring the software. Let’s take a moment to walk through the settings so you can see what each one will mean to deployment. Here’s what you’ll see:
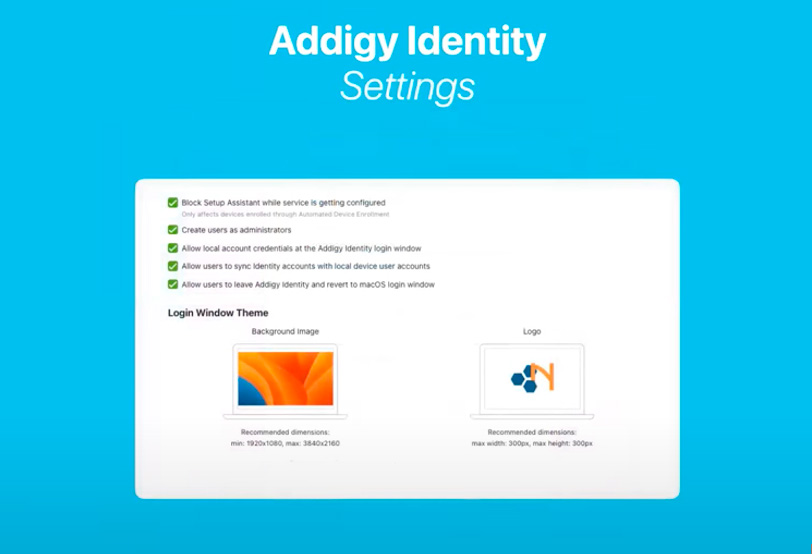
Block Setup Assistant While Service Is Getting Configured
This setting is specific to new, out-of-the-box devices. This setting ensures that when you deploy Addigy Identity via Automated Device Enrollment (ADE), the Apple Setup Assistant will pause and hold the user on the enrollment screen until Addigy Identity has been fully deployed. This pause prevents end-users from setting up their local account before Addigy Identity is deployed and ready to handle their authentication via Microsoft, Google, or Okta.
Create Users as Administrators
This setting determines if the users created via the just-in-time user account creation are administrators or standard users. Our approach at Ntiva is to allow and encourage people with Macs to run as managed admins. This is only possible because we support zero-touch, Automated Device Enrollment. However, if your in-house security team isn’t comfortable with this arrangement, those users can be created as “standard users” instead. If you have a mixed batch where some users should be admin and other standard users, we recommend leaving this option off and elevating privileges via other methods.
Allow Local Account Credentials at the Addigy Identity Login Window
This setting and the final option to “Allow Users to Leave Addigy Identity and Revert to macOS Login Window” allow users to bypass Addigy Identity.
Essentially, these settings serve as failsafes that allow your users to access their machines even if they’re offline. It is important to note that allowing users to bypass the identity provider means they can bypass password syncing and password policies. For high-security environments, it may be required to leave this option off.
Allow Users to Sync Identity Accounts With Local Device User Accounts
One of the advantages of Addigy Identity is that it makes login and authentication a more effortless, more seamless experience. Unchecking this box forces the user to create a new account.
Generally, this is not recommended, but it makes sense in some cases. For example, if you’re setting up a computer lab where you have a local administrator but want to ensure no student or other team member can take over the account, you might disable this setting. Otherwise, we recommend leaving this box checked.
Allow Users to Leave Addigy Identity and Revert to macOS Login Window
As mentioned above, this setting provides a failsafe that allows users to access their machines even if they can’t access the internet. We generally offer this option to ensure nobody is locked out of their computer if, for example, they’re traveling and have unreliable internet access.
Login Window Theme
Finally, you can establish your login window theme from these settings. If you’d like to choose a particular background image or display your logo on your machines, we’re happy to help! We’ll send you the specs, and you can send us the logo to drop in for your users.
Additional Resources to Learn More About Addigy Identity for Apple Authentication
Addigy Identity is an excellent tool for workplaces that need an authentication solution for Apple devices that streamlines the process for users without sacrificing security. The software can be configured and synced with Microsoft 365/Azure, Google, and Okta, and we’ve created helpful walkthroughs for the two most popular login experiences.
|
Microsoft 365 / Azure |
|
| Read our step-by-step guide to the Microsoft/Azure login experience here. | Check out this step-by-step guide to the Google login experience here. |
Why Your Users Need Stronger Passwords in a Single Sign-On World
While Apple may not always be transparent about its plans for the future, we’re confident that Addigy Identity will continue to be an excellent tool for providing a true single sign-on experience. But as the sign-on process is streamlined, it will be more critical than ever that your users create strong passwords.
We may want to retire the phrase “password” from our lexicon and begin thinking about long passphrases and sentences instead. Since your team members will be using a single passphrase to get full access to your system, it’s more important than ever that they choose one that’s secure.
Want to learn more about Microsoft IT Support for your business? See Ntiva’s Microsoft IT Support Services.
Managed Services for Microsoft 365
Microsoft OneDrive IT Services
Back to blog

.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)


