
In the past, using strong passwords was enough to keep accounts secure and hackers at bay. This is no longer the case, and cyber security services require a lot more than just a solid password. Hackers are becoming more devious and highly sophisticated with their techniques, especially through email-based cyber attacks like spear phishing.
Spear phishing tactics are being used every day to steal sensitive data and personal information from innocent people. You might consider yourself too smart to fall into a phishing email trap but try not to feel overly confident that you won’t someday fall prey and get “hooked” by a phishing hacker.
GET THE GUIDE: HOW TO SPOT AND PREVENT PHISHING ATTACKS!
Table of Contents:
- Spear Phishing is on the Rise
- What is Spear Phishing?
- Spear Phishing: Real World Examples
- Phishing Prevalence for Individuals and Businesses
- The Job Market is the Latest Spear Phishing Target
- Best Methods for Preventing Spear Phishing Attacks
Spear Phishing is on the Rise
An alarming 75% of organizations around the world experienced some kind of successful phishing attack last year, and phishing incidents nearly doubled in frequency, from 114,702 incidents in 2019 to 241,324 incidents in 2020. We can expect this trend to continue, which means that you and your entire team need to be aware of the threat, and hyper-vigilant in prevention efforts.
Clearly, this is one of the most successful hacking methods of our time and the effects of phishing on businesses and individuals can be detrimental. CEO fraud, credit card fraud, and even domain fraud will continue to be a problem as long as people continue to fall for phishing's tricks.
The good news is that there are ways to stop phishing in its tracks - you just have to know how to protect yourself.
The methods we’ll cover here can help to prevent even the most well-executed spear phishing campaign from resulting in company data theft.
What is Spear Phishing?
You probably have a vague understanding of phishing and whaling attacks, but vague isn’t good enough if you plan on staying protected. Even if you thoroughly understand phishing, spear phishing is a more sophisticated version of the traditional email hacking practice.
Similar to old-school phishing techniques, spear phishers attempt to gain access to specific individuals' usernames and passwords by simply asking for sensitive information. They do this by posing as a source you can normally trust (like your bank, cell phone provider, or personal Amazon account). There is, however, one major difference between traditional phishing and spear phishing.
Norton Security says that spear phishing “takes this trick to the next level, using social engineering. Spear phishing effectively uses all the data that’s on the Internet and social media about you to lull you into an inappropriate sense of comfort before attempting to get your personal details.”
Even as an IT service provider, we receive these emails all the time!
Spear Phishing: Real World Examples
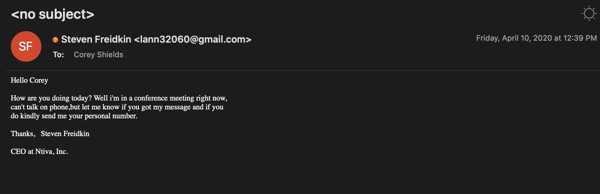
Notice the email pictured above. This email was sent to multiple departments, with many employees getting the same message from our CEO. Notice the mismatched <gmail.com> address in the "From" line, the odd personalization, and the appearance of being rushed?
These are telltale signs of spear phishing attempts.
They're trying to get us to react quickly in fear that we missed something from the CEO. Prying on fear using the names of real people you work for is exactly why phishing works.
Within minutes, our internal IT team was alerted, and this sender was blocked. No breach occurred, and we went back to our normal work with no interruptions. With some personalized training, your business can become this resilient as well!
Phishing Prevalence for Individuals and Businesses

As you can see from the facts and stats below, phishing attempts are extremely prevalent - so yes, it could potentially happen to your email address if you don’t take cybersecurity seriously.
- According to the 2019 Internet Security Threat Report from Symantec, 71.4% of targeted attacks on individuals involve spear phishing emails.
- According to the 2019 Checkpoint Research Security Report, 82% of manufacturers experienced a phishing attack that year.
- Dashlane Blog found that the average cost of phishing attacks on mid-sized companies in 2018 was $1.6 million.
Phishing incidents have been on the rise and that trend will continue. These shocking numbers say it all, but the first step to protect from a data breach and theft is awareness, so you’re already making progress.
The Job Market is the Latest Spear Phishing Target
We all know, cybercriminals included, that the job market is heating up. We at Ntiva have seen evidence of this in the form of spear phishing through resume responses complete with job offers.
This newest method involves an email saying "we like your resume and would like to look at hiring you full-time, but we'll need some personal information to conduct a full background check and proceed."
To show how savvy these cybercriminals are becoming, these emails are sent saying "our IT department or HR department will contact you shortly, but in the meantime, we'll need your home address, social security number, and checking account number for direct deposit."
The emails often include legitimate links to the company's LinkedIn page and even contact info for the real HR department. By the time you realize what has been done, they will have all the info they need.
So, for those seeking new employment, here are a few things to keep in mind:
- No company is going to offer you a job on the spot through email.
- You will never receive a job legitimate corporate job offer from a Gmail account
- If you receive this type of email, do not respond, reach out directly to the company's HR department
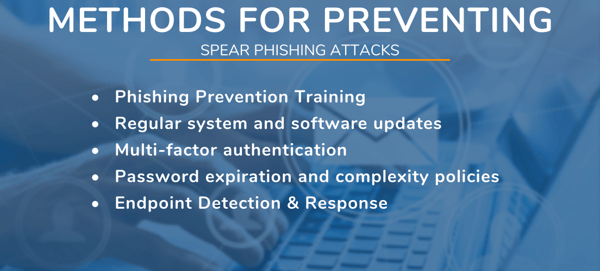
Best Methods for Preventing Spear Phishing Attacks
As we mentioned before, awareness is a major aspect of spear phishing prevention, but it’s not the only way to keep your company protected from phishing, ransomware attacks, and other cyber threats.
Here are some of the best recommendations!
1. Provide Ongoing Employee Training
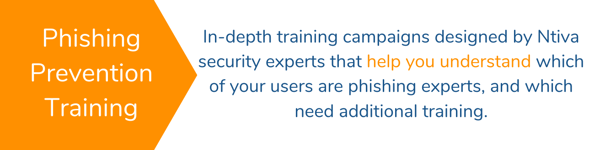
Over 90% of IT security incidents start with phishing attacks against employees, so it’s no surprise that the best prevention method is through end-user training.
A phishing hacker is only successful when the victim clicks on a link or downloads a file. Once that happens, the cybercriminal is in and it’s too late. The good news is that the ball is entirely in the user’s court, and there’s no risk of a breach if the link isn’t clicked or the file isn’t downloaded.
Investing in phishing prevention training for your employees is one of the most successful prevention techniques out there. This will not only teach your employees the basics of phishing attacks and what they look like but also provide guidance as phishing hackers evolve and become even more sophisticated over time.
2. Keep All Systems Current with the Latest Security Patches and Updates
It’s easy to overlook something as common as automatic updates. We all click that “Install Later” button out of habit, but the truth is, we’re leaving our software and systems vulnerable to attack when we do this.
Configure any software you can (including your operating system) to install updates automatically. Make sure to shut down your machine when you’re done for the day so ensure that the updates install properly, and you’re ready to go with a fresh PC in the morning!
3. Require Your Employees to Use Multi-Factor Authentication
Using MFA is one of the simplest and most cost-effective methods of enhancing email security. MFA adds an extra layer of security by requiring an additional “factor” for logins. It most commonly works as a push notification sent to a mobile device with a verification code that is needed for logging in. No extra end-user security software needed.
MFA helps to keep your business protected from ransomware and stops phishers in their tracks. It’s just one method to reduce the risk of a security breach, but it’s one you should never do without.
4. Implement a Security Policy to Address Password Expiration and Complexity
Many organizations already have a password complexity requirement in place due to regulatory compliance, but even without regulations, you should set stringent password requirements, both for expiration and complexity.
When it comes to passwords, people will always try to use the simplest password possible, and when they’re prompted to change, they’ll simply put in the same password with another number at the end. You can prevent this from happening by allowing no repeated passwords. Just make sure your employees don’t start writing down their passwords on sticky notes!
Addressing password expiration is important because it limits the ability of a cybercriminal to access an account for a long period of time. If passwords are set to expire every 45 days, this will prevent a thief from being able to return to an account with stolen credentials in the future to steal even more data.
5. Deploy Endpoint Detection & Response on Every System
Gone are the days of installing antivirus software the day you get a computer, never to touch it again. Endpoint Detection & Response (EDR) is the next step in cybersecurity.
EDR lives on each user’s computer, automatically detecting and stopping potential attacks that have slipped by your antivirus software. EDR detects activity quickly and contains the adversary before they can move laterally through your network.
Using sophisticated AI, EDR monitors and stops complex attacks, like those that may be launched by a spear-phishing email, automatically behind the scenes. Isolating the machine when any abnormal activity is detected, EDR can literally save your entire business.
There is no mail filter in the world that will stop spear phishing attacks. Cybercriminals have worked hard to obtain as much information about you as possible. The only way to stop them is to be educated. The steps we’ve listed above will keep your entire organization, and the client data you possess, safe.
If you’re interested in learning more about the tactics being used by cybercriminals check out our latest guide, “How to Spot And Prevent Phishing Attacks” below!
Back to blog
.png?width=1300&name=Phishing%20Guide%20CTA%20(1).png)

.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)


