
No matter what security protocols your company puts in place or how unbreakable you believe your password to be, there is one vulnerability that cybercriminals can always exploit.
You.
Instead of hacking devices or accounts to gain access, cybercriminals are hacking humans, you, me, all of us; through phishing attacks, imposter scams, and other social engineering methods.
In fact, according to this year's CyberSecurity Hub Report, 75% of respondents cited social engineering/phishing attacks as the top cybersecurity threat at their organization. These attacks rely on human error rather than system or software vulnerabilities, which means that responsibility lies with the individual and the organization to safeguard against them.
As a result, organizations must take the lead in ensuring that their employees know what a social engineering attack looks like, how to identify red flags, and are informed about common threat tactics. These steps are critical to protecting yourself and your business.
Table of Contents
What is Social Engineering?
How Does a Social Engineering Attack Work?
How Social Engineering Attacks Happen
6 Common Types of Social Engineering
How to Identify (Most) Types of Social Engineering Attacks
How to Protect Your Business From Social Engineering Attacks
What is Social Engineering?
Social engineering usually involves some form of psychological trickery, fooling well-meaning users or employees into breaking standard security rules. Most attacks are delivered through email or other communication methods designed to lure victims into handing over sensitive data by appealing to them in a psychologically manipulative way.
For example, an attacker might pose as a coworker with an urgent problem that requires otherwise off-limits resources or a boss that expects an immediate response to a request. By appealing to a target in a manner that invokes an emotional response like fear, urgency, or vanity, the fraudster tricks them into letting their guard down and breaking their security protocol.
As a result, these attacks can be remarkably efficient and difficult to prevent.
How Does A Social Engineering Attack Work?
A social engineering attack is relatively easy for a hacker to pull off; hook one distracted, stressed individual and persuade them to do what they (the hacker) ask.
When these attacks work, they work beautifully.
The list of cautionary tales is endless and grows almost every day. Earlier this year, a phishing attack designed to steal Microsoft 365 credentials was carried out by hackers impersonating the US Department of Labor. These hackers impersonated the DoL's email address and domain, used official DoL branding and letterhead, and directed its victims to a fake website for bidding that required their M365 logins.
Scams like these are evidence of just how convincing these attacks are becoming.
While it's easy to see how even a loyal, cautious employee could fall for an attack like this-it's worth remembering that, with the right email security measures in place, these attacks would not be successful.
How Social Engineering Attacks Happen
A social engineering attack can be delivered through email, phone, social media, or even in person. But no matter what channel is used for the attack, the methods are always the same.
The attacker poses as an individual who has a legitimate need for the information they are seeking; for example, they might pose as an employee's supervisor looking for login information to a password-protected file.
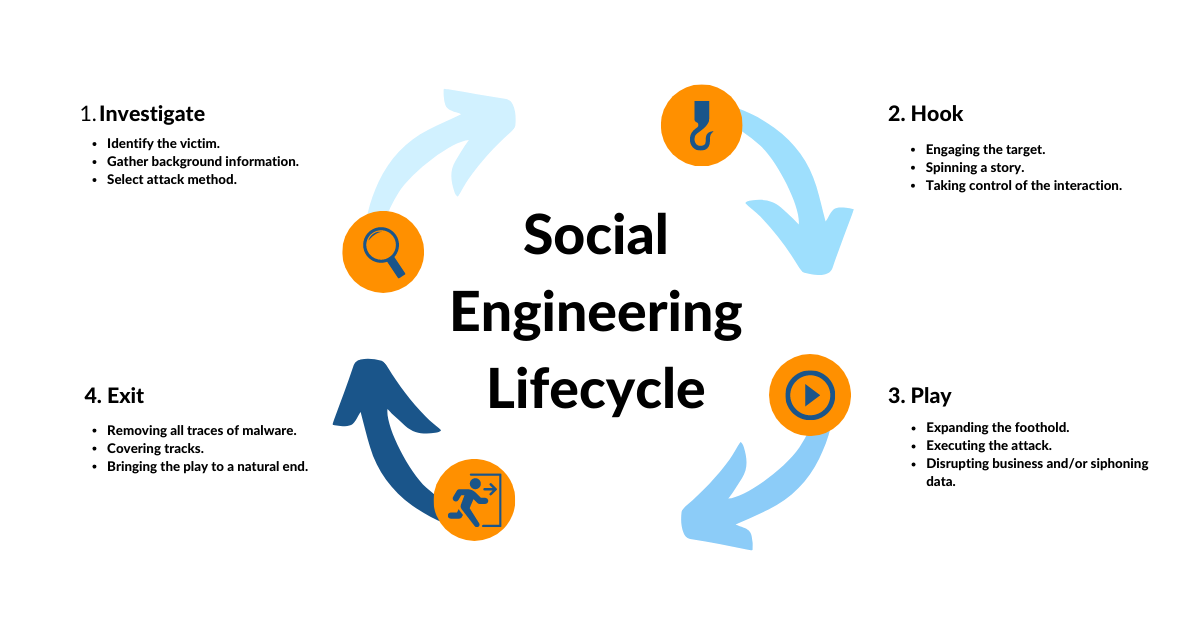
Social engineering attacks typically follow these steps:
Investigate: The attacker identifies victims and chooses a method of attack.
Hook: The attacker makes contact and begins the process of establishing trust.
Play: The attack commences, and the attacker collects the information or payment.
Exit: The attacker covers their tracks and concludes the attack.
1. Investigate:
Scammers begin by identifying potential victims of their attacks. They gather background information on their targets in order to make sure that they have access to credentials, money, or data that are "worth stealing."
Next, they search for their victims online in order to gather personal information about the target that will allow them to gain credibility with them. The more the attacker knows about their victim, the more likely that person is to let their guard down, setting the stage for a successful breach.
2. Hook:
Now it's time to engage the target. The scammers will use email addresses, phone numbers, and social media accounts to get in touch and try to open the door to an attack.
Then, they pitch the target with a "hook" to get them interested. This could be an offer to interview for a job, an online freebie, etc.
These hooks can seem harmless and risk-free, so why not play along?
3. Play:
Next comes the "play," the point at which the attacker lures their target into the scam. For instance, if you click a link to apply for a job online, the attacker secretly installs malware on your device, infecting your entire network. Next thing you know, your company's sensitive data has been stolen; in seconds.
A simple mistake like this can cost businesses millions of dollars. Think about it: the average cost (in 2022) of a company data breach is $4.35 million!
4. Exit:
As soon as the attackers have completed their play, they'll vanish. All traces of malware will be removed, and any evidence that they were there will disappear. In the meantime, it may be months before the breach is discovered, and by then, the attackers will have escaped detection entirely.
6 Common Types of Social Engineering
1. Phishing
Phishing campaigns are a scam in which the attacker sends a fake email that appears to be legitimate. So legitimate, in fact, that your spam filter probably won't stop it. It might appear to be a message reputable or trusted source, like a representative from your bank.
This fraudster could claim to have important information regarding your accounts but ask you to verify your identity with personal data such as your social security number, account number, and birthdate. Once you have provided this information (to the fake bank officer), they have managed to steal your private data, and the phishing attack has taken place.
Spear phishing is a targeted phishing attack. In these cases, the threat actors have done more research and are seeking out a particular user to target. This is done by gathering more specific information about that individual, often through their online profiles and digital footprints. The victim of a spear phishing attack is more likely to fall for the scam because of the more personalized nature of the outreach.
Whaling is another targeted phishing scam that targets high-value (so-called "big fish") individuals like C-levels in an organization.
2. Vishing and Smishing
Vishing and smishing scams are similar to phishing attacks and use similar manipulative techniques, but use phone calls and text messages rather than email.
Vishing (voice phishing) happens when a scammer tries to trick someone into disclosing sensitive information or giving them access to data over the telephone.
One of the most common vishing schemes involves the attacker calling victims and pretending to be from the IRS or a collection agency. The caller threatens the victim in an attempt to gain personal information or compensation. These scams most often target older individuals, but anyone can fall for these scams if they are not properly trained.
Smishing is phishing via the use of SMS text messages. It’s easy for scammers to purchase spoofed phone numbers and attack targets with malware links blasted through text messages.
RELATED READING: SMISHING - YOUR GUIDE TO SMS PHISHING
3. Pretexting
Unlike phishing emails, which use fear and urgency to their advantage, pretexting attacks rely on building a false sense of trust with the victim. This requires the attacker to build a credible story that leaves little room for doubt on the part of their target.
Pretexting occurs when someone misuses their role or creates a fake persona. It is usually what happens when data breaches come from inside an organization. A scammer may be impersonating a trusted person, possibly with authority (a CEO, IT tech) in order to gain access or information.
For example, Edward Snowden famously gained access to company passwords while acting as a systems administrator. His victims respected his title and gave him the access he requested,
4. Baiting
Baiting (or clickbaiting) capitalizes on human nature and the innate desire to satisfy our curiosity or get something for free, for example. Something as simple as a free music download or a gift card can lure a user into sharing their credentials in a corrupted environment.
Or, what about an opportunity to view a video link of an accident or a three-head baby? These offers tempt users to click and, once again, introduce malware into their systems.
5. Tailgating and Piggybacking
Tailgating attacks involve someone without proper authentication gaining physical access to a restricted space by following an employee into the building.
In a common type of tailgating attack, a person impersonates a delivery driver and waits outside a building. When an employee gains security's approval and opens their door, the attacker asks that the employee hold the door, thereby gaining access from someone who is authorized to enter the company.
Piggybacking is similar to tailgating, except that in this scenario, the authorized user is aware and allows the other individual to "piggyback" off of their credentials.
6. Quid Pro Quo
Quid pro quo (Latin for 'something for something) is a social engineering tactic in which the attacker attempts a trade of service for information. One of the most common types of quid pro quo attacks involves fraudsters who impersonate IT support personnel and spam call as many direct numbers that belong to a company as they can find.
These attackers offer IT assistance to each user, for example, by promising a security update in exchange for the employee disabling their AV program. The fraudster then installs malware rather than the expected security updates.
How to Identify (Most) Types of Social Engineering Attacks
A social engineering attack can come in many different forms (email, text, voice call, social media post, etc., but most of them have the same traits. And while all of these traits are found in legitimate communications, if three or more can be found in a single message, chances are it is a scam.
- The message is unexpected. We all get unexpected messages every day (look at your inbox!), but a scam email is always unexpected. Depending on the sophistication of the attack, it could be a scammer who knows you are applying for a new mortgage; so the fraudulent message requests sensitive information and asks for it with a swift deadline attached.
- The request is out of the ordinary. Is this a request from someone you know asking for something unusual? In most cases, social engineering requests ask the potential victim to do something they have never been asked to do before. It might be a request to send money, open a document, or give information you’ve never been asked about in the past.
- The message includes a sense of urgency. Most scams include a heightened sense of urgency, in order to induce stress. Communicating a threat of harm (financial, physical work-related, etc.) induces the potential victim to act quickly and without caution.
- The request could cause harm. This could be a request to open a document, download a program, send information, or input a password. All of these are examples of potentially harmful actions.
- The communication includes an unusual file or URL. Most social engineering scams include a rogue link or file to download. For example, a scam email request may simply request the potential victim to send back personally identifiable information (e.g., “We need your bank account information”, “Send us your SSN”, etc.), but most include potentially dangerous URL links, documents or content.
If you receive a message with three or more of these high-risk traits, then stop, review and make sure it is not a social engineering scam before continuing.
How to Protect Your Business From Social Engineering Attacks
More often than not, social engineering attacks target your business or employer in hopes of stealing sensitive information and data. So, what steps can you take to protect your team and your company from social engineering attacks?
- Commit to ongoing security awareness training.
- Regularly test your team with simulated attacks.
- Keep your website, applications and hardware updated.
- Set up data monitoring.
- Create a positive security culture.
At Ntiva we can set you up for success and deploy the right security solutions to protect your business and your employees from social engineering attacks. Reach out to learn more!
Back to blog




-1.jpeg?width=420&height=280&name=AdobeStock_446756617_Editorial_Use_Only%20(1)-1.jpeg)
-1.jpeg?width=420&height=235&name=AdobeStock_763411872%20(2)-1.jpeg)

.png?width=420&height=420&name=Blog%20Hero%20-%20Square%20(1).png)