.png?width=360&height=180&name=Email%20Security%20HERO(1).png)
As you browse through our IT services, blog posts, and company info, you’ll quickly see just much we emphasize the importance of cybersecurity here at Ntiva. We’re not trying to scare you, but the fact of the matter is that it takes much more to stay secure these days.
This is especially true when it comes to email security. Whether you’re using Outlook email, Gmail, or other, keeping your account secure against malware, spam, phishing, and other sophisticated email-borne threats requires action on your part.
In this complete guide to email security, we’ll cover everything you need to know about protecting your email, including:
- Email Security Definition
- Why Is Keeping Email Secure So Important?
- How Secure Is Email?
- What Are Email Security Policies?
- End-User Email Security Best Practices
Email Security Definition
Email security is the broad term used to describe all of the different practices and procedures for protecting email accounts and the content within them.
There are many components to email security including tools and techniques such as encryption, multi-factor authentication, password protection, employee security training, and more.
Why Is Keeping a Secure Email So Important?
Maybe you don’t even realize it, but your email holds a lot of sensitive information. Bank accounts, personal details, sensitive company facts and figures… it’s all there in your inbox.
This is why email (especially Microsoft Outlook since it’s the most prevalent enterprise email provider) is the main target for attackers trying to infiltrate a company network.
It’s also why it’s so important to take the right security steps.
CIO.com says that enterprise email security is too often overlooked, and “organisations tend to spend big bucks on endpoint and network security solutions but end up neglecting email security, despite the fact 90% of cyberattacks are perpetrated via email.”
How Secure Is Your Email?
Email is one of the most effective forms of communication for SMBs and major enterprises. It was designed to be highly accessible to make open communication within and between organizations more of a possibility.
 But we all know that accessible and open can also mean insecure. The open format of email means that anyone who intercepts a message can view it, which is a major problem for organizations that send sensitive information.
But we all know that accessible and open can also mean insecure. The open format of email means that anyone who intercepts a message can view it, which is a major problem for organizations that send sensitive information.
You should never rely solely on the email service provider to keep your information safe, there are many additional layers you need to add on to keep your email protected.
Phishing is still considered to be the number one way that emails get hacked. According to the SANS Institute, 95% of all attacks on business networks are the result of successful spear phishing attacks.
In other words, a human opened an email and either clicked on a link or opened a file that they weren’t supposed to.
In addition to phishing, business email compromise (BEC) - which you can think of an impersonation fraud - is another critical issue. In a BEC scam, hackers send an email message that appears to come from a known source making what looks to be a legitimate request.
An example is an email that looks like it's coming from a vendor that your company regular deals with, but contains a bogus invoice. Or a company CEO appears to be asking his or her assistant to purchase a dozen gift cards. Falling for one of these scams can result in big financial consequences.
Note that both of these tactics are preying on busy or distracted employees, so don't overlook email security training which you'll learn more about below.
Read up on how to protect against phishing in Microsoft Office 365 here!
What Are Email Security Policies?
Every organization should have a certain set of email-related policies for employees to follow. These are basically just rules that are enforced to keep sensitive and confidential company info from getting into the hands, but also to protect each employee individually.
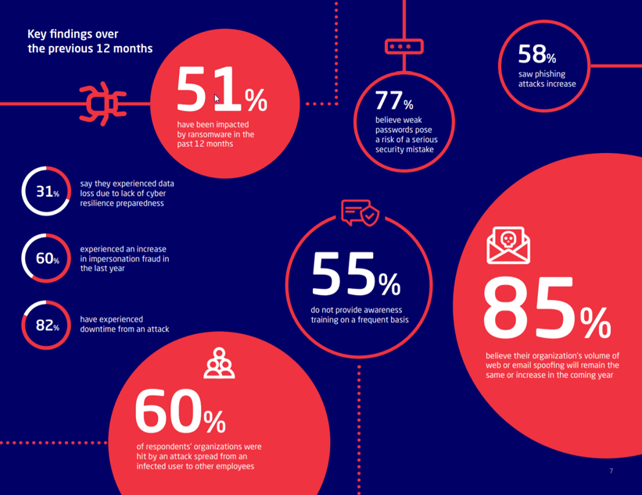
Email Security Key Findings (Source: Mimecast, The State of Email Security 2020)
We’ll go more in-depth into some of these next, but here are a few examples to give you an idea of important policies to include in your email security plan:
- Your company email account is for business use only and should only be used on the company network
- Changing email passwords must be done every 90 days
- Every employee must attend yearly cybersecurity training
- Two-step authentication is required for email account logins
Remember, these are just examples. The specifics of your email security policies are up to you, but just be sure to cover all the bases - it’s better to be more thorough than not thorough enough so that your employees never have to read between the lines.
End-User Email Security Tips & Best Practices
The very first step in email security is to create a game plan. You should have a detailed plan in place for the entire company, but also encourage your employees to take extra security steps for even more protection.
Here are a few more things you should be doing for enhanced email security:
1. Provide Regular Cybersecurity Training & Education
Email security education shouldn’t just be for CIOs, administrators, or IT experts - it should be for everyone. Training your employees and keeping the company up-to-date on cybersecurity is one of the best investments you could ever make.
The mistake that so many companies make is to offer a one-and-done course and then never give training another thought. No matter how thorough and comprehensive that course was, cyber threats like email phishing are constantly evolving, which means that security education needs to be an ongoing thing.
2. Establish Unbeatable Passwords
If you’re using a password like “123456” or “password123”, stop reading and change your password NOW. Even if you’re using your dog’s name followed by your birthday, please, just go change it. Each of your passwords should be unique, and it’s best if you include a combo of numbers, special characters, lowercase and uppercase letters.
Changing passwords frequently and using a unique sequence of letters, numbers, and symbols is the easiest way to improve Office 365 security or protect a Gmail account.
3. Use Two-Factor Authentication (2FA)
There’s a very good chance you’re already doing this since 2FA is common for signing into most online applications and services nowadays. It works by adding in an additional “factor” so that the only person logging into an account is the account holder and not one of the bad guys.
Note that Two-Factor-Authentication is often used interchangeably with Multi Factor Authentication (MFA).
4. Avoid Public WiFi Networks
Your online information becomes way more vulnerable when you connect to a public network. Cyber predators love to lurk on coffee shop WiFi, so avoid opening your email if you’re not on a private, secure network.
If you’re out and in desperate need of checking an email that was just sent by your boss, by all means, go ahead, just be sure to do it on your phone using your cellular data plan, not WiFi.
The Takeaway on Email Security
Aside from these best practices, just try to have some common sense. Backup and archive your Outlook email, never open suspicious emails, files, or URLs, and be smart about password protection.
The takeaway here is that you need layered defenses for comprehensive protection of your company (and the same goes for personal) email accounts.
We’re here to help, so get in touch today to learn about email security services to start developing a foolproof cyber security plan.
Back to blog



.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

