
The U.S. Department of Defense (DoD) published Cybersecurity Maturity Model Certification 2.0 (CMMC 2.0) in November 2021 to safeguard sensitive national security information. CMMC 2.0 replaces CMMC 1.0 as the framework designed to protect the U.S. defense industrial base from increasingly frequent and complex cyberattacks.
CMMC 2.0 is different from CMMC 1.0 in four key ways. Here’s what your organization needs to know.
Table of Contents
CMMC 2.0
Key Change 1: Simplified Model
Key Change 2: Different Requirements at Each Level
Key Change 3: Assessments
Key Change 4: Flexibility
How Ntiva Helps You Achieve CMMC 2.0 Compliance
Want more in-depth info on CMMC and all of your business cybersecurity needs? Be sure to register here for the Cybersecurity for the Rest of Us webinar series!
CMMC 2.0
CMMC 2.0 is the next iteration of CMMC, the DoD’s cybersecurity training, certification and third-party assessment program.
Want to learn more? Read all of Ntiva's GovCon blogs here!
The DoD created the CMMC model to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) that the DoD shares with contractors and subcontractors through acquisition programs:
- Federal Contract Information is not intended for public release. The DoD provides this information to help contractors and subcontractors develop and deliver products and service to the federal government.
- Controlled Unclassified Information is information that the government creates or possesses (or that an entity creates or possesses on behalf of the government) that must be handled using safeguarding or dissemination controls required by law.
Key Change 1: Simplified Model
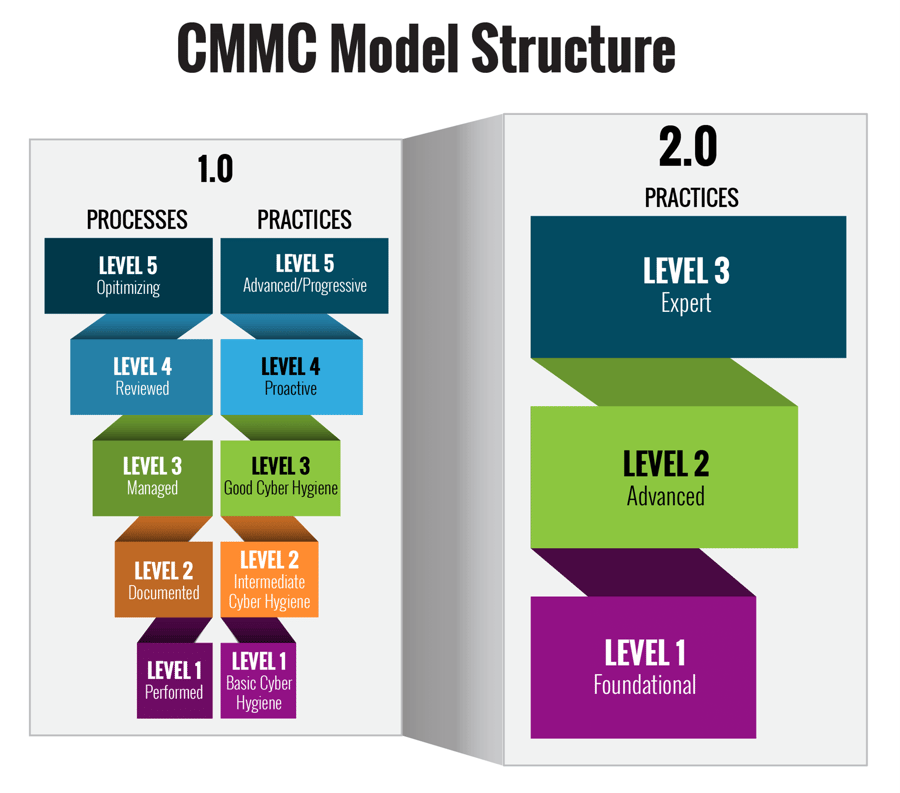
“The first major difference between CMMC 2.0 and CMMC 1.0 is a simplified model,” says Dr. Jerry Craig, Chief Information Security Officer, Ntiva.
He goes on to add, “CMMC 1.0 featured five increasingly progressive levels of processes and practices, from Basic to Advanced. Levels 2 and 4 acted as transition stages between Levels 1, 3 and 5.”
CMMC 2.0 reduces these five levels down to just three: Foundational, Advanced and Expert. These three levels are also increasingly progressive.
- Foundational / Level 1. Corresponds with Level 1 in CMMC 1.0
- Advanced / Level 2. Corresponds with Level 3 in CMMC 1.0
- Expert / Level 3. Corresponds with Level 5 in CMMC 1.0
Key Change 2: Different Requirements at Each Level
CMMC 1.0 required cybersecurity standards and maturity processes at each level. Cybersecurity standards consisted of requirements from NIST SP 800-171 as well as standards unique to CMMC.
CMMC 2.0 eliminates all maturity processes, and it replaces all CMMC unique security practices with NIST standards:
- Advanced / Level 2 mirrors NIST SP 800-171 (110 security practices)
- Expert / Level 3 is based on a subset of NIST SP 800-172 requirements
Related Reading: Cybersecurity Maturity Model Certification (CMMC) Datasheet
Key Change 3: Assessments
With CMMC 1.0, self-assessments and self-attestations were not sufficient at any of the five CMMC 1.0 levels. CMMC 1.0 required a CMMC Third Party Assessment Organization (C3PAO) to assess a defense contractor’s cybersecurity maturity and to then issue a certification of CMMC compliance. This certification was for the level that corresponded to the contractor’s internal cybersecurity controls.
“CMMC 2.0 changes all this by allowing defense contractors to demonstrate compliance on their own without any third-party assessments,” says Dr. Craig.
“Contractors can now conduct annual self-assessments of Foundational Level compliance. Advanced Level self-assessments will also be possible for a number of ‘non-prioritized’ acquisitions that require Advanced Level CMMC 2.0 certification.”
.png?width=150&name=Jerry%20White%20BG(1).png)
– Dr. Jerry Craig, CIO, Ntiva
Third-party assessments are now only required for high-priority procurements that carry with them national security implications. These typically involve Advanced Level certification.
Key Change 4: Flexibility
CMMC 1.0 was notorious for not providing a particularly flexible implementation approach. It required contractors to implement 100% of their security practices before they could be assessed as compliant with the requirements of any of the five levels.
CMMC 2.0 give contractors greater flexibility.
Contractors, for example, are permitted to make Plans of Action & Milestones (POA&Ms) for achieving certification at a given level and within a specified time period. To do this, they must achieve a minimum score to support CMMC certification with POA&Ms.
CMMC 2.0 also allows contractors to obtain a waiver to its requirements when the work being undertaken is deemed mission-critical.
How Ntiva Helps You Achieve CMMC 2.0 Compliance
If you are like many defense contractors, you lack the skills and resources in-house to address the requirements of CMMC 2.0, particularly NIST SP 800-171 Rev. 2 and SP 800-172. One way to meet these CMMC 2.0 cybersecurity requirements is to outsource your compliance initiative to a Managed Security Services Provider (MSSP), such as Ntiva.
An MSSP with expertise in CMMC 2.0 offers four critical services that help you prepare for a CMMC rollout:
- Readiness Assessment and Gap Analysis. Uncovers systems and processes that may not meet the standards outlined in NIST 800-171.
- Remediation Plan. A prioritized, actionable plan of record to address any security gaps uncovered in the Readiness Assessment and bring you into CMMC compliance.
- Monitoring and Reporting. MSSP monitors, detects, and reports on cybersecurity incidents within your systems.
- System Security Plan. Documents information about each system in your environment that stores or transmits CUI.
CMMC 2.0 has been described as essentially a “leaner and more flexible version of CMMC 1.0.” It’s easier to understand, easier to implement and more flexible. If you need help putting CMMC 2.0 to work for your organization, read CMMC 2.0: A Comprehensive Guide for DoD Contractors.
Back to blogAbout the author
.png?width=320&height=320&name=Jerry%20White%20BG(1).png)
Jerry is Ntiva’s Sr. Director of Security and CISO, offering more than 20 years in the IT and cybersecurity industry. Certified CISO, CISSP and CCSP, Jerry also serves part-time as Adjunct Professor in the University of Maryland Global Campus.
.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)


