
By now, most government contractors are aware of the upcoming Cybersecurity Maturity Model Certification (CMMC). This comprehensive guide will show you how to prepare, achieve, and maintain CMMC 2.0.
Table of Contents - Guide to CMMC 2.0
2. Contractors That Will Require CMMC 2.0
3. An Overview of the CMMC 2.0 Model
6. Contractors that will Require CMMC Level 3
8. CMMC 2.0 Outsourcing Benefits
9. The Purpose of a CMMC 2.0 Gap Analysis and Readiness Assessment
10. Creating a CMMC 2.0 Remediation Plan
11. Ongoing Cybersecurity Monitoring and Reporting
12. Building and Updating the System Security Plan (SSP)
13. Outlining the CMMC Audit Process
14. CMMC Dates and Milestones for DoD Contractors
15. CMMC Compliance Checklist: Next Steps
16. How Ntiva Can Help With CMMC 2.0
1. CMMC Compliance Explained
The CMMC is the latest security framework mandated by the Department of Defense (DoD) for any contractor that does business with the DoD.
Its guidelines specify a range of security maturity levels that must be met and will be used by the DoD as a qualification criterion for requests for proposals (RFPs) and vendor selection.
IT security for government contractors has always been a hot topic, but this recent change from the DoD has made maintaining compliance with security regulations even more important.
The CMMC aims to mandate strict compliance by DoD providers. Contractors who do not meet CMMC standards may find themselves shut out of DoD business.
The initial version of the CMMC framework was rolled out in January 2020, followed by CMMC 2.0 in November 2021. This version is available on the DoD CMMC website.
A memorandum of understanding (MOU) between the DoD and the CMMC Accreditation Body (CMMC-AB) was signed. Although certification, licensing, and training requirements for assessors and organizations were established, continued delays in the official pilot and go-live phase continue to interrupt the program’s deployment and requirements.
The Defense Federal Acquisition Regulation Supplement (DFARS) currently provides administrative acquisition policies and procedures for the DoD, and applies to all DoD contractors.
With the regulatory process to update the DFARS-7012 requirements still pending, the plan for CMMC requirements in RFPs was delayed to 2024 or beyond.
While some of the more than 300,000 DoD contractors will have the staff, resources, and expertise to meet their CMMC requirements in-house, many will not.
Fortunately for those in the latter group, managed security service providers (MSSPs) such as Ntiva are developing specialized programs to help assess contractors’ current capabilities, create remediation plans where necessary, and conduct ongoing cybersecurity monitoring and reporting.
2. Contractors That Will Require CMMC 2.0
The short answer is that anyone in the defense contract supply chain will require CMMC compliance. The DoD estimates the rollout of CMMC 2.0 standards will affect over 300,000 aerospace and defense suppliers.
According to the DoD, “CMMC is intended to serve as a verification mechanism to ensure appropriate levels of cybersecurity practices and processes are in place to ensure basic cyber hygiene as well as protect controlled unclassified information (CUI) that resides on the Department’s industry partners’ networks.”
The cybersecurity challenges faced by the DoD are enormous. For context, the Pentagon stops an estimated 36 million emails containing ransomware and phishing attacks every day.
Despite these best efforts, in late 2018 the Pentagon reported a data breach exposing the personal information of 30,000 DoD employees on a system operated by a third-party contractor.
2020 opened with the Department of Homeland Security warning of a possible increase in cyberattacks against government networks due to rising tensions in the Middle East.
Government cybersecurity is a never-ending battle, and is predicted to only get more complex!
Back in 2015, the DoD identified specific cyber requirements in the DFARS (252.204-7008 and 252.204.7012).
DFARS required DoD contractors to adopt cybersecurity processes and standards created by the National Institute of Standards and Technology (NIST). All government contractors needed to prove that they had implemented the requirements of the NIST SP 800-171r2 as of December 2017.
This framework was part of the broader government initiative to protect the DoD supply chain from cyber threats and other security risks.
The adoption of the framework has been slow, despite DoD efforts to incentivize supplier compliance. The DoD has expressed concern that most defense industry contractors maintain only adequate security hygiene practices.
Faced with unacceptable risks to CUI stored on contractor systems, the DoD introduced the CMMC to ensure that appropriate cybersecurity protections and processes are in place.
What sets the CMMC apart from “business as usual” under the NIST SP 800-171r2 protocol is a strict audit and certification process that will establish compliance as a condition of doing business with the Defense Department.
CMMC 2.0 replaces the current “self-attestation” model with third-party certification allowances. The audit and certification process establishes compliance with DoD conditions.
With the launch of CMMC 2.0 in November 2021, DoD contractors received information from the DoD and the CMMC-AB that the rules on third-party audit requirements were being relaxed. It was estimated that somewhere between 40,000 and 80,000 contractor organizations would be able to self-attest versus being required to obtain a third-party certification.
Defense contractors were also told that the “all or nothing” or “pass/fail” audit process was changing to include the introduction of Plans of Action and Milestones (POA&Ms). However, it’s still unclear how many POA&Ms an organization may be allowed to submit, if there will be a severity level assigned, or if multiple POA&Ms combine for higher severity findings.
In early 2022, the DoD made multiple announcements indicating that the governance and oversight of the CMMC program was being moved under the DoD’s Office of the Chief Information Officer (CIO). Shortly thereafter, articles were published stating that self-attestation at CMMC 2.0 Levels 2 and 3 would not be allowed, thus returning the requirement for formal third-party audits and certifications.
The logic behind the announcement was that virtually all information outside of federal contract information (FCI) would be considered CUI, and virtually all contractors would need access to some CUI. Therefore it made sense to require third-party audits for all contractors operating at these levels of the CMMC model.
While there is no evidence this statement is accurate or not, many speculate that removing the third-party audit requirement effectively returned the program to the state that existed prior to the implementation of the CMMC, where contractors self-attested under DFARS clause 252.204-7012. Returning to this previous state does not provide additional protections to the DoD, as it defaults to a sort of honor system.
Additional concerns have been voiced by CMMC registered provider organizations (CMMC RPOs) and certified third-party assessor organizations (C3PAOs) over the resources spent to position themselves to assist the DoD with audit requirements. However, there’s been no indication of a change in the accreditation structure.
Under the current structure, CMMC RPOs and C3PAO are 2 of 7 entities classified in the CMMC ecosystem by the CMMC-AB. The other 5 include:
- C3PAO candidate (pending CMMC ML3 assessment)
- CMMC provisional assessor (PA)
- CMMC registered practitioner (R.P.)
- Licensed partner publishers (LPP)
- Licensed training provider (LTP)
These classifications exist to address the specific needs of organizations seeking CMMC certification (OSC), using a database to match them with suitable providers who can help them through specific steps in the certification process.
For clarity’s sake, the capabilities of CMMC RPOs versus C3PAOs are outlined below:
|
CMMC RPO |
C3PAO |
|
Offers cybersecurity consulting to prepare for CMMC assessment |
Performs CMMC assessment and evaluates compliance |
|
Advises on plan of action for attaining and maintaining certification |
Determines level of certification (1-3) |
|
Does not conduct official certification assessments unless also classified as a C3PAO |
Employs certified CMMC Assessors to conduct assessments |
According to the DoD, any organization intending to meet CMMC 2.0 Levels 2 or 3 will be required to pass a third-party or government-led assessment process. Self-assessments will suffice to meet CMMC Level 1 requirements.
In addition, we recommend attempting to pass with no POA&Ms in case the DoD shifts positions back to its original requirements. The DoD intends to establish score minimums and baselines as well as specify a small subset of requirements that cannot be on a POA&M in support of achieving a CMMC certification. However, these contract limits have not yet been announced.
There are cases in which relying on a POA&M may prohibit a contractor from passing an audit before contract award, and if that contractor runs into time, resource, or funding constraints late in the process when a POA&M is determined to be unallowed, it may not be awarded the contract.
Finally, without knowing how many third-party auditors will be available, how long an audit will take, or how long it might take to be re-assessed for failed practices, the risk of relying on a POA&M to pass the audit may be too high for most organizations.
3. An Overview of the CMMC 2.0 Model
The most current CMMC model framework is CMMC 2.0, which was announced in the second half of 2021 and officially published in December 2023.
CMMC 2.0 defines cybersecurity practices at the highest level by domains, and each domain is then segmented into practices, also commonly referred to as controls, which are mapped into groups of capabilities. Capabilities identify contractor achievements that ensure cybersecurity objectives are met within each domain.
DoD contractors will demonstrate compliance with required capabilities by showing adherence to practices and processes that have been systematized across the three maturity levels of CMMC.
Practices measure the technical activities necessary to achieve compliance with a given capability requirement, while processes measure the maturity of a company’s processes.
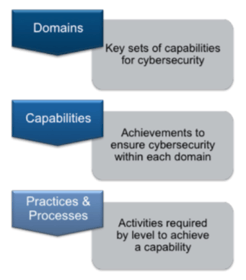 Source: CMMC Version 1.02
Source: CMMC Version 1.02
4. The 3 Levels of CMMC 2.0
The CMMC model has three defined levels, each with a corresponding set of practices necessary to pass the assessment. Practices range from basic cyberhygiene (Level 1) to more advanced capabilities (Level 3). Contractors must meet associated practice criteria to achieve each specific CMMC level.
The following insights compare several features of the original CMMC iteration (“V1”) to those of CMMC 2.0 (“V2”):
- V2 eliminated Levels 2 and 4 from the V1 framework. They were initially intended as transition stages between Levels 1, 3, and 5 in the V1 model.
- V2’s Level 2 aligns closely with the previous Level 3, while V2’s Level 3 aligns closely with the previous Level 5.
- V1 had 17 cyberdomains, while the updated V2 has 14 (more on CMMC domains shortly—see Section #5).
- Despite having a considerable role in V1, processes have been removed as an official requirement under V2.
Below is a visual representation of the CMMC Version 1 model that contained 5 levels (on the left), compared to the updated CMMC 2.0 model that contains 3 levels (on the right):
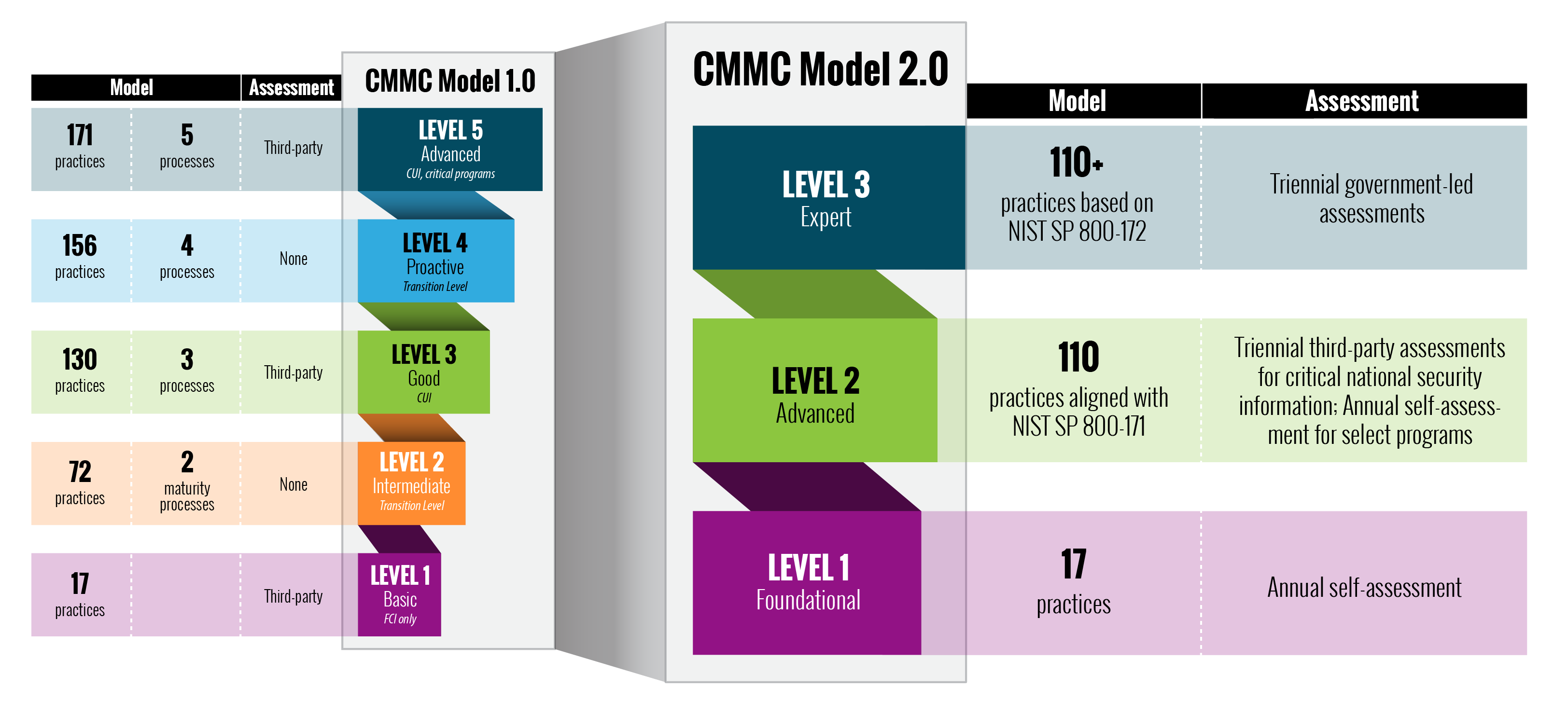
Source: OUSD
5. Understanding CMMC Domains
The CMMC 2.0 model consists of 14 domains. Many of these CMMC domains originated from the Federal Information Processing Standards (FIPS) 200 security-related areas and the NIST SP 800-171r2 control families.
Below is a brief summary of the domains, but you can find more information on each domain and additional details in the CMMC Compliance Checklist for DoD Contractors.
CMMC 2.0 also includes Asset Management, Recovery, and Situational Awareness domains.
CMMC Level 2 requirements apply to defense contractors who create or access CUI.
Level 2 focuses on the protection of CUI, plus encompasses all the security requirements specified in NIST SP 800-171r2.
Any contractor with a DFARS clause in its contract will need to meet at least Level 2 requirements. Note that DFARS clause 252.204-7012 applies and specifies additional requirements beyond NIST SP 800-171r2 security requirements, such as incident reporting. The 14 domains and their compliance requirements are as follows:
- Access Control (AC): Establish who has system access, control that access, and limit data access to authorized parties.
- Awareness and Training (AT): Implement and regularly execute security awareness training programs for all employees.
- Audit and Accountability (AU): Have a process in place to document CUI access and perform secure audits of those logs to ensure accountability.
- Configuration Management (CM): Establish configuration baselines as a measure to judge the efficiency of your systems.
- Identification and Authentications (IA): Ensure the proper roles have the correct level of access that can be reliably authenticated.
- Incident Response (IR): Have an incident response plan in place to detect and report events, implement responses to incidents, and test responses to measure emergency preparedness.
- Maintenance (MA): Develop a maintenance system that can sustainably and effectively operate your systems.
- Media Protection (MP): Provide proof of media identification and access along with evidence that media protection protocol, sanitation protocol, and transportation protection are in place.
- Personnel Security (PS): Ensure proper screening of all personnel and provide evidence that CUI remains protected during personnel activity.
- Physical Protection (PE): Provide evidence of the physical security surrounding your assets to clearly illustrate that they are protected.
- Risk Assessment (RA): Determine possible risks facing your company through regular risk assessments and vulnerability scanning for both internal and external personnel.
- Security Assessment (CA): Implement a system security plan (SSP) to manage controls and perform periodic code reviews.
- System and Communications Protection (SC): Outline the security requirements of all systems and channels to prove control of communications at system boundaries.
System and Information Integrity (SI): Identify and address flaws within a system, identify hazardous and malicious content, and monitor your network and systems.
6. Contractors That Will Require CMMC Level 3
CMMC Level 3 was originally the third certification for defense contractors out of five possible levels, as outlined above.
Specifically, Level 3 requirements apply to defense contractors who create or access CUI.
Level 3 focuses on the protection of CUI and encompasses all of the security requirements specified in NIST SP 800-171r2, along with 20 additional practices to mitigate threats.
Any contractor with a DFARS clause in their contract will need to meet at least Level 3 requirements. Note that DFARS clause 252.204-7012 applies and specifies additional requirements beyond NIST SP 800-171r2 security requirements, such as incident reporting.
7. How To Get CMMC Certified
DoD contractors who have the necessary IT staff and resources may choose to prepare CMMC cybersecurity certifications in-house.
NIST created a guide, the Self Assessment Handbook—NIST Handbook 162, as an aid for suppliers self-directing their certification initiative. The handbook details certification requirements for NIST SP 800-171r2, which aligns with CMMC Level 2.
Unfortunately, there is no self-assessment guide currently available for NIST SP 800-172r2. A draft of the 172 specifications, however, can be found here.
Before proceeding with an in-house CMMC program, contractors should consider the stakes—especially the need to pass the third-party CMMC audit on the first try.
If the initial examination is unsuccessful, contractors stand to lose significant time and money while correcting any security shortcomings. They may also encounter hold-ups due to a potential backlog of audits, especially in the early days of CMMC.
As CMMC certification becomes a requirement for contract awards, such delays could prove costly for companies who count on DoD business for a considerable portion of their revenue.
8. CMMC 2.0 Outsourcing Benefits
Notably, many DoD contractors may lack the skills or resources to address the requirements of NIST SP 800-171r2 or SP 800-172.
For those organizations, an effective means to meet the CMMC 2.0 cybersecurity requirements is to outsource their compliance initiative to a qualified Managed Security Services Provider (MSSP) such as Ntiva.
Experienced MSSPs have the necessary processes and templates in place to undertake a gap analysis and create the overall security plan. They also have the available resources and expertise to complete remedial activities if required, plus the tools necessary to monitor security performance, resolve issues, and provide detailed reporting.
As a result, defense contractors may find that outsourcing (rather than independently building) these capabilities saves significant money and time.
You should also confirm that an MSSP is a CMMC RPO.
Organizations given the CMMC RPO seal are deemed “cyber-knowledgeable,” possessing a good understanding of CMMC requirements and protocols.
In the following sections, we detail 4 critical activities that a qualified MSSP or CMMC RPO can perform to help prepare DoD contractors for a CMMC 2.0 assessment:
- Readiness Assessment and Gap Analysis
- Remediation Plan
- Monitoring and Reporting
- System Security Plan
9. The Purpose of a CMMC 2.0 Gap Analysis and Readiness Assessment
The gap analysis and readiness assessment are foundational steps for contractors looking to gain a detailed understanding of how close they are to meeting the requirements of their targeted CMMC level.
A readiness assessment helps uncover systems and processes that may not meet the standards outlined in NIST SP 800-171r2, answering essential questions such as:
- How is data stored and access to information controlled?
- Are incident response plans in place, current, and effective?
- Are IT staff and other personnel adequately trained?
- How are security protocols implemented and maintained?
The resulting gap analysis pinpoints risk areas for contractors and facilitates the creation and execution of the Remediation Plan, either by the MSSP or by utilizing in-house resources.
Without an exhaustive gap analysis in hand, DoD contractors will find it challenging to identify risks, prioritize activities, and determine costs for any remedial steps required for attaining CMMC 2.0 certification.
10. Creating a CMMC 2.0 Remediation Plan
A remediation plan is a prioritized, actionable plan of record to address any security gaps uncovered in the readiness assessment and bring the DoD contractor into CMMC compliance.
This official process to mitigate risks and identify weaknesses in CMS systems is illustrated in a POA&M, which will document:
- The weaknesses found, with description: Each area of non-compliance (from Access Control to Media Protection) must be identified and assigned a unique priority level as it corresponds to each NIST SP 800-171r2 practice (a.k.a. control).
- An overall remediation plan for each non-compliant practice: This plan should provide an approximate timeline for resolution (including a recommended remediation date), name the parties responsible for completion, and identify any training or resources required.
- A general risk rating: Although they aren’t prioritized under NIST SP 800-171r2, each of the 110 security requirements must be considered and are weighed against predicted system impact to determine the level of risk.
Impact on the DoD’s Supplier Performance Risk System (SPRS) score: The associated value of every requirement not met is deducted from 110. This can result in a negative score (as low as -203) because high-risk controls are weighted based on fundamental Basic Security Requirements set by the DoD.
11. Ongoing Cybersecurity Monitoring and Reporting
Once the DoD contractor has completed the remediation and is CMMC compliant, it will need to regularly monitor, detect, and report on cybersecurity incidents within its own systems.
These activities require specialized tools and expertise, often placing an administrative burden on many contractors. This is another key reason why many contractors will opt to outsource this task to an MSSP who specializes in cybersecurity.
12. Building and Updating the System Security Plan
The SSP is a living document that must be updated when a company makes substantial changes to its security profile or associated processes.
Typical information captured in the plan includes company policies, employee security responsibilities, network diagrams, and administration tasks.
For NIST SP 800-171r2 and CUI requirements, the SSP must document information about each system in a contractor’s environment that stores or transmits CUI. The SSP also details the flow of information between systems and authentication and authorization processes.
The DoD mandates a review of DoD contractors’ SSPs as part of the awards contest. Without a current SSP in place, contractors may not be awarded DoD business.
While creating and updating the SSP is critical to maintaining certification requirements, it can be a resource-intensive process, so defense contractors must ensure they have the resources in place for this undertaking.
13. Outlining the CMMC Audit Process
While the DoD has not finalized all details of the audit process for every level, here is what has been confirmed to date:
- Most if not all DoD contractors will need to become CMMC Certified by passing a CMMC audit (subject to change). The CMMC-AB recommends that you start at least 6 months in advance.
- This will validate that the contractor has met the appropriate level of cybersecurity for its business with the DoD.
- Certification will become a requirement for any organization that wishes to hold Department of Defense contracts or act as a subcontractor on DoD-related projects.
- The DoD will employ C3PAOs to conduct audits on DoD contractor information systems and verify that DoD contractors have met the appropriate level of cybersecurity controls.
- Based on the audit results, contractors will be awarded the applicable certification (from Level 1-3) if they meet the requirements of 100 percent of the controls for that level and all lower levels.
- Level 3 cybersecurity requirements must be assessed by government officials, but these audit details are still under development.
- While third-party organizations will normally perform assessments, some higher-level evaluations may be performed by DoD assessors within the Services, the Defense Contract Management Agency (DCMA), or the Defense Counterintelligence and Security Agency (DCSA).
DoD Statement on the Assessment Process
“Your organization will coordinate directly with an accredited and independent third-party commercial certification organization to request and schedule your CMMC assessment. Your company will specify the level of the certification requested based on your company’s specific business requirements. Your company will be awarded certification at the appropriate CMMC level upon demonstrating the appropriate maturity in capabilities and organizational maturity to the satisfaction of the assessor and certifier.”
Office of the Under Secretary of Defense for Acquisition & Sustainment — Cybersecurity Maturity Model Certification
14. CMMC Dates and Milestones for DoD Contractors
DoD contractors have been anxiously awaiting the start of official CMMC assessments, which are currently expected to go through a 5-year phase-in period for select pilot contracts. Disagreements regarding program structure, an inability to solidify program rules and the rulemaking process, whether POA&Ms will be permitted, whether contractors can self-attest at Level 2, and other logistical decisions resulted in significant delays to the program’s official rollout. As of March 2023, the DoD is processing the results of the 60-day period allocated for interested parties to comment on the proposed rule. This process is expected to take at least several months, indicating a final rule release sometime in late 2024.
December 2023
CMMC 2.0 is officially published, with assessments estimated to start in the first quarter of 2025. The 2-month timeframe to officially comment on the changes concluded at the end of February 2024. According to Washington Technology, “the Defense Department now has to process and respond to the [nearly 300] comments before it issues the final version of the industry-wide rule in the fall.”
February 2022
During a Feb. 10 town hall, Deputy DoD CIO David McKeown said “further analysis has shown all 80,000 will require third-party assessments. This reverses the previous updates from November 2021 where the DoD implied that potentially half of the contractors (~40,000 of 80,000) seeking Level 2 compliance would be permitted to self-attest. This comes after the announcement that the CMMC Program was being moved under the Office of the CIO.
November 2021
CMMC 2.0 is officially announced. Major changes include:
- The CMMC model changed from 5 levels to 3 levels, effectively eliminating the CMMC Version 1.0 Levels 2 and 4.
- The possible introduction of POA&Ms, eliminating a 100 percent pass/fail model.
- The potential for ~40,000 of the ~80,000 contractors expecting to need Level 2 certification the ability to forego a C3PAO audit and instead self-attest.
September 2021
The DoD announced that it will not be enacting the final rule that would have cemented the implementation of CMMC in September 2021 as planned. This enactment is then pushed out until "late 2021."
March 2021
DoD contractors will need to be certified by an accredited Assessor to qualify to bid on new projects. Because CMMC will not be applied retroactively on existing contracts, the current DFARS 7012 requirements will be in place through 2026.
September 2020
On September 28, 2020, the DoD released interim cyber-related DFARS rule changes that will go into effect on Nov 30, 2020. You can read more about it in our latest post on NIST SP 800-171.
The initial round of audits will launch for a limited number of DoD Programs with the required CMMC levels specified. Contractors will need to be certified to the appropriate CMMC level to receive the RFP for those programs. It's believed that only the companies submitting for these RFI/RFPs will be eligible for CMMC assessment in the initial stages.
February-July 2020
Training for the first round of assessors is being developed. Certification exams, job descriptions, and levels of assessors are all in development. Check out the CMMC Accreditation body for updates.
January 2020
Official CMMC Levels and requirements are released.
15. CMMC Compliance Checklist: Next Steps for Contractors
Whether or not DoD contractors choose to prepare for the CMMC in-house or outsource to an MSSP, there are key activities they should undertake to stay ahead of the transition.
You will also want to check out our “CMMC Compliance Checklist” for a breakdown of the CMMC 2.0 framework by domain, as it illustrates the exact requirements per domain. Some general requirements are listed below:
- Assess the current organization for NIST 800-171r2 compliance. NIST 800-171r2 requires that contractors “periodically assess the security controls in organizational systems to determine if the controls are effective in their application.”
- Create or update the System Security Plan (SSP). NIST 800-171r2 also mandates contractors to document and regularly update SSPs, including information such as company policies, network diagrams, and relationships with other systems.
- Build the Plan of Action & Milestones. The POA&M will document the remediation project plan and help establish timelines and resource requirements.
- Implement the Remediation Plan. Completing the POA&M will ensure compliance with NIST 800-171r2 and existing contracts while preparing for the full CMMC 2.0 rollout.
Maintain Compliance. Maintaining compliance with DoD security standards can be a complex undertaking and is often overlooked. It requires a documented plan and frequent (sometimes daily) activities.
16. How Ntiva Can Help With CMMC 2.0
Submission of a proposal to the DoD—as a prime or sub—requires that you have an SSP and POA&M that documents your cyberpractices against NIST SP 800-171r2 and shows a clear plan for addressing any gaps.
Haven’t done it yet? In addition to likely being in violation of your DoD Terms & Conditions, your business is not ready for CMMC 2.0 rollout.
One of the first steps you should take is to perform a CMMC Readiness Assessment and Gap Analysis. The Ntiva Security Team will assess your process, policies, and systems; develop an SSP and POA&M; and give you a documented plan of what needs remediation to pass your CMMC 2.0 audit.
Click on the image below to learn more about how we can help you get ready for NIST and CMMC 2.0!
Back to blog
About the author
.png?width=320&height=320&name=Jerry%20White%20BG(1).png)
Jerry is Ntiva’s Sr. Director of Security and CISO, offering more than 20 years in the IT and cybersecurity industry. Certified CISO, CISSP and CCSP, Jerry also serves part-time as Adjunct Professor in the University of Maryland Global Campus.
.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)


