.png?width=360&height=180&name=Apple%20MDM%20HERO(1).png)
Yesterday, @SentinelOne published their findings on "XcodeSpy", a new form of malware targeting macOS.
You can read it here: "New macOS malware XcodeSpy Targets Xcode Developers".
It was only a matter of time before the Apple ecosystem was targeted in a similar way to GitHub and other code repositories that can be shared among developers and sysadmins.
Criminals have added trojans (backdoors) to some shared Xcode projects, making it imperative to take action if you develop code/tools using these types of shared repositories.
The problem?
No anti-malware tools are currently able to detect this, yet, because it’s so new.
The good news?
If you don’t develop any code on your Mac or use shared code repositories, you don’t need to worry about this, just yet.
If you do build code using these repositories, are there any tools out there to protect you?
Yes, thanks to Patrick Wardle and Objective-See, who recommends his *free* tools to fill the gap until endpoint detection tools catch up:
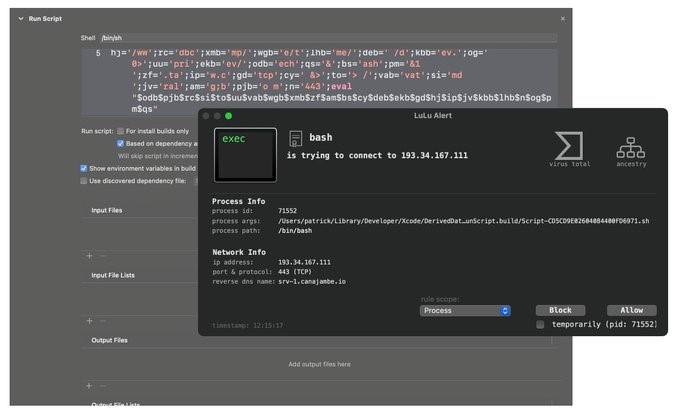
 LuLu will detect and notify you of any outbound requests to a malicious command and control server (via /bin/bash):
LuLu will detect and notify you of any outbound requests to a malicious command and control server (via /bin/bash):
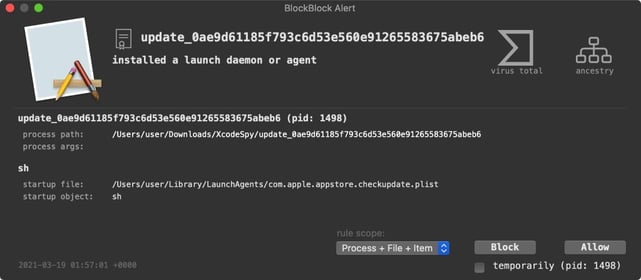
 BlockBlock will alert you if you allow the malicious payload (EggShell), to be downloaded from the server - right when it attempts to persistently install itself as a Launch Agent:
BlockBlock will alert you if you allow the malicious payload (EggShell), to be downloaded from the server - right when it attempts to persistently install itself as a Launch Agent:
We’re keeping a close eye on XcodeSpy and will post more updates as information becomes available!
Don't Take a Chance with Your Apple Cybersecurity
Interested in working with a team of true Apple experts with the right tools and the knowledge and support skills you need? Click below to learn more:
Back to blog



.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

