
Microsoft Office 365 is unique in terms of information security. As the productivity platform where your team gets most of their work done, it represents a trove of data that attackers would be happy to get their hands on. Here are 5 best practices to help you protect your data!
Think about all the applications within Office 365 that you use on a daily basis. Outlook email, Excel and Word are probably the most popular, so lets take a look at the risks associated with each:
- Email access through Outlook lets attackers spam people on your contact list, send phishing attacks, and harvest any important attachments you may have sent.
- Excel files include critical data on payroll and accounting, and many companies use them (unwisely, in our opinion) to store customer data.
- Word docs are the mother-lode – they contain contracts, expansion plans, patent documents, and other intellectual property than an attacker can exploit.
Those are just 3 examples out of many!
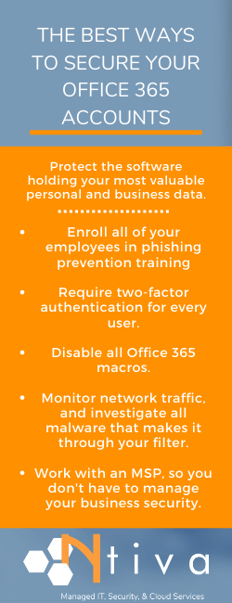
So what are the best ways to secure your Microsoft Office 365 account?
Read on to get some good advice from an IT consulting company who deals with these issues across hundreds of clients every day!

Tip 1: Know Your Enemy
The first step towards defending your Office 365 implementation is knowing how your enemies will try to attack it.
The most common method is some kind of account takeover attack – this means that an attacker is going to try and steal one of your employees’ login credentials.
With the credentials in hand, an attacker can perform any of the actions above, either stealing the information connected to the account, using the account access to plant vulnerabilities and find malware, or usually some combination of both.
The most common vector for an account takeover attack is a phishing email. Phishing emails are surprisingly effective nowadays – one in seven of your employees will open a phishing email, and even a single phishing email can wreak havoc on your organization..
If your attackers are aiming at Office 365 specifically, their phishing email will usually look as though it comes from Microsoft. It might say something like, “there’s a problem with your account billing, click here to fix it.”
Once you click the link, you’ll be presented with a website designed to look like the Office 365 login screen. If you’re fooled into putting in your credentials, the attackers will immediately take over your account.
Phishing prevention training is a must for all employees, and should be delivered on a regular basis. We'll dive into that a bit more in Tip #3 below!
Tip 2: Understand Malware and Ransomware
In addition to account takeover attacks, there are also malware and ransomware to consider. Many criminals consider it so easy to steal from companies using deception that malware rarely comes into the picture – but if they do choose to deploy malware, watch out.
About 93 percent of malware is polymorphic, meaning that it regularly changes its signature to avoid detection by antivirus software.
In addition, ransomware no longer just affects on-premises files. Cloud implementations are also vulnerable. Even if all of your Word, Excel, and PowerPoint documents are stored online, or if you store your documents in a Microsoft Azure volume, these files are still vulnerable to encryption.
If an attacker chooses to use malware against you, they’ll often – ironically enough – pose as a colleague and send an infected Microsoft Word file.
Upon opening the file, the word document will use a complicated system of macros to download ransomware into your file system and begin wreaking havoc. Using Microsoft Word to distribute malware is the most common exploit found in malware.
You should be justly frightened of these attacks. They are very effective, and criminals use them often, with nearly every business experiencing an attempted cyberattack every year. Once you know about these methods, however, it is that much easier to defend against them.
Tip 3: End-User Training Can Save Your Business
Your first step when it comes to protecting Office 365 from ransomware is to immediately disable macros.
A macro is basically a text shortcut – a custom string that tells Word or Excel files that if you type in the word “signature” (just for example), then the word will auto-populate with your email signature. This is helpful if you often need to write and customize boilerplate text, but attackers can also use this feature to run and generate code.
Disabling macros shuts down the most common attack vector found in ransomware strains.
Even if you shut down Word macros, there are still ways for attackers to use malware to infect Office 365. No matter which method they choose, however, most of them will still use the same entry point – phishing emails.
This means that Phishing Prevention Training – training your employees to recognize and avoid phishing emails – will be an important component of your defense.
Phishing emails have some commonalities that make them easy for trained employees to spot. For example, an email may look like it comes from Microsoft, and the word “Microsoft” might be in the sender’s address, but there will almost certainly be something off.
The URL might end in “.cm” instead of “.com,” or it might come from “microsoftoffice367,” but no matter what, there will be a telltale clue. Training employees to recognize these and other signs will make them up to 50 percent less likely to click on a phishing email.
Of course, there’s no kind of training that can make your employees 100 percent effective against phishing emails. Therefore, phishing prevention training needs to be used in concert with other techniques.
- Installing advanced behavioral-detection antivirus and keeping it up to date
As we’ve mentioned, most malware is polymorphic, meaning that it evades signature-based detection. Behavioral detection helps evade this problem – instead of looking for a specific signature, it looks for processes related to unauthorized creation, deletion, modification, or encryption of files. This way, you’ll avoid polymorphic malware and even malware taking advantage of previously unknown “zero day” vulnerabilities. - Placing your antivirus solution in line with Outlook
The one problem with cloud-based email clients is that much of the action takes place outside your firewall. In other words, it’s possible for one of your users to receive a phishing email, click on a link, and download a suspicious attachment before your security tools ever get involved. Companies need to invest in security tools that they can extend to their webmail clients, ensuring that any downloaded attachments get scanned before they reach a user’s endpoint. - Updating email filters to exclude known bad senders
One surefire way to prevent attackers from succeeding at phishing attempts is to make sure that their phishing emails never reach your users’ inboxes. One way to do this is to use an email filter that is constantly updated with known fraudulent domain names. While Office 365 does this automatically to a certain extent, you can also specify junk mail rules at the server level, the group level, or the level of the entire organization. Once an email is identified as junk, users will be unable to click on any links in the message or reply to it. - Analyzing any phishing emails that make it past your filters
The goal of phishing protection in Office 365 is that administrators shouldn’t have to do much work themselves – even if you customize your email filters, you’re still only tweaking a series of rules that Microsoft has already put in place. Therefore, if an email gets past the filters that both you and Microsoft have set up, it’s worthy of study. Administrators can use a free tool called Decent Security to study phishing emails, understand how it got past their filters, report it, and then update their filters so that the sender can never target your organization again.
Using all of these methods together won’t get you to 100% protection against malware, but it will get you very close. Once you incorporate measures against account takeover attacks, you’ll get even closer.
Tip 4: Use Stronger Passwords
Phishing attacks aren’t just used to spread malware – they’re also used to steal user credentials.
As we’ve mentioned, users will receive an email prompting them to log in to a service, they’ll get directed to a fake website for that service, and then they’ll lose their credentials once they log in to that service.
If you’re following the guidelines in the previous section, you’ll have a decent chance against phishing attacks – both the kind that drop malware, and the kind that attempts to steal user account credentials.
Unfortunately, this kind of phishing attempt isn’t the only way for an attacker to take over an employee’s login information.
For example, employees have a bad habit of reusing passwords. Over half of employees use the same password across multiple accounts, both personal and work-related. What’s likely to happen is that one of your employees will use a low-security service that gets hacked. Their email and password associated with this hack will live on the internet forever.
Any attacker who wants to try to break in to one of your Office 365 accounts will simply take the password that’s been breached and try to see if it’s been used anywhere else. More than likely, they’ll be able to score a hit.
<<WATCH OUR WEBINAR: Password Best Practices for Your Business>>
Other common password-stealing methods include:
- Trolling employee social media to find the name of a person’s dog, their mother’s maiden name, their best friend’s name, and other common password-retrieval methods.
- Credential-stuffing a low-security application with an attack that guesses hundreds of thousands of variations on low-security passwords.
- Physically entering your office (while disguised as a FedEx delivery person) and swiping post-it notes from various monitors.
To put it mildly, if an attacker wants an employee password from your organization, it’s only a matter of time before they get one.
Fortunately, there are a few ways of stopping these account takeovers. The best way is multi-factor authentication, also known as MFA.
Tip 5: Implement Multi-Factor Authentication
Multi-factor authentication (MFA) works on the idea that because no password is safe from attackers, you need to use something extra to authenticate your identity. This can be something like a one-time password that’s generated via an app on your phone, a physical USB key that you put inside your computer, or a biometric like your fingerprint or a retinal scan.
Attackers – unless they are fantastically skilled or persistent – have no way to account for this extra authentication step. As a result, MFA is fantastically effective. A recent study from Google shows that MFA, when implemented using a dedicated authenticator app, will prevent 100 percent of bulk phishing attacks and 90 percent of targeted spear phishing attacks.
Even using an SMS authenticator – which is vulnerable due to the possibility of an attacker intercepting a one-time password when it’s sent over text – will still prevent 76 percent of targeted attacks.
Office 365 is designed to make setting up MFA simple. First, find the left navigation pane in the admin center, and click on “setup.” Then, find the “sign in and security” section. You’ll see an option that says, “turn on multi-factor authentication.” Click on “view.”
This will take you to a page called “Make sign in more secure.” Navigate to “get started” and then select the checkboxes that say, “require multi-factor authentication for admins” and “require users to register for multi-factor authentication and block access if risk is detected.”
If you want to make two-step verification even more secure, you can set up secure USB keys for multi-factor authentication. Microsoft works with a variety of partners, including FIDO and Yubikey, that allow administrators to procure and setup USB keys for use with Office 365.
In addition, a tool called Windows Hello lets administrators set up biometric security using third-party fingerprint readers and facial recognition cameras. In short, Office 365 has built-in tools that can let you implement security that even a spy agency would be proud of.
These tips can be a lot to handle. Who has time to schedule company-wide end-user training? How can you be sure that everyone has enabled MFA on their Office 365 account? Do you have an IT team big enough to actually provide real-time network monitoring?
Here at Ntiva, we provide comprehensive Managed IT Services, and work with companies across industries to provide comprehensive IT security. From consulting with you to create an IT security plan to implementing policies, procedures, and technology, we can provide Office 365 consulting that protects both your users and customers.
If you’d like to schedule a consultation, click below. We can’t wait to work with you!
Back to blog



.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

