
It’s easy for businesses to get overwhelmed when it comes to figuring out what they need for adequate cyber security protection. We recommend that the very first thing you do is a security risk assessment - we've put together 4 steps to get you started.
Why You Need A Cybersecurity Risk Assessment
Most businesses, especially small to medium businesses, are in a challenging position when it comes to cyber security protection.
Your clients and partners may well have the expectations that you have enterprise-grade security in place, which in the past has been difficult if not impossible to afford.
All the media hype around major security data breaches has not helped - consumers want and expect to be protected no matter who they are doing business with.
Depending on your industry, you may also have to take into consideration regulatory requirement needs, which will be an important part of your cyber security strategy.
You want the best cyber security protection possible, but it's often hard to figure out how to prioritize with a limited budget.
What should you focus on first in the risk assessment process?
In order to make an educated decision, you need to start with a security risk assessment.
That's why we're providing some steps you to can take on your own, keeping in mind that a formal risk assessment performed by a cyber security services expert will go much deeper than the check list we're providing.
Cybersecurity Risk Assessment in 4 Simple Steps!
Step One: Understand Your Data
The first step in any data risk mitigation strategy is “understanding your data,” which is fundamental to every cyber security program.
What do we mean by understanding your data?
Well , people can’t steal what you don’t have, so eliminating any unnecessary data you have hanging around is super important.
To do this, you need to understand where your sensitive data is, how long you need to keep it, and who really needs to access it - often way too many people have access to data they simply don't need.
Documenting all this is not a fun task, but eliminating the storage of unnecessary data, and restricting access to it, are two of the most basic things you can do in reducing risk.
Step Two: Understand Your Risks
When a consultant works on a formal cyber security risk assessment, they typically draw on risk management frameworks such as the NIST cyber security framework.
NIST is a standardized security framework that was created to help improve security operations for government agencies as well as public and private organizations.
However, the NIST framework was primarily designed for large federal systems or organizations with big budgets, and is unsuitable for most smaller businesses.
What you CAN do is use these frameworks to create a simplified plan, while maintaining the intent of the guidelines as much as possible, and that's what we're going to provide you with.
There are 3 terms you need to understand and think about before you begin this.
- Threats. This can be an attacker or a hurricane. An identified threat is something that could negatively impact your business.
- Vulnerabilities. This is a gap in your protection that potentially allows a threat to harm you, e.g. an unlocked door or lack of a firewall.
- Risks. This is the likelihood that a threat can exploit a vulnerability. For example, an identified risk would be having the chance of having a virus infect your computer due to a lack of anti virus software.
Now let's move on to assessing your risks and conducting the actual risk assessment.
Step Three: Security Risk Assessment Cheat Sheet
Below is a high level cheat sheet which lists some of the most important items you need to think about when doing your own risk assessment.
The answers to these questions will help you define what you need to protect, and how much you need to spend to do it.
This cheat sheet is backed up by an audio guide that will provide you more information, so keep on scrolling down to learn more!
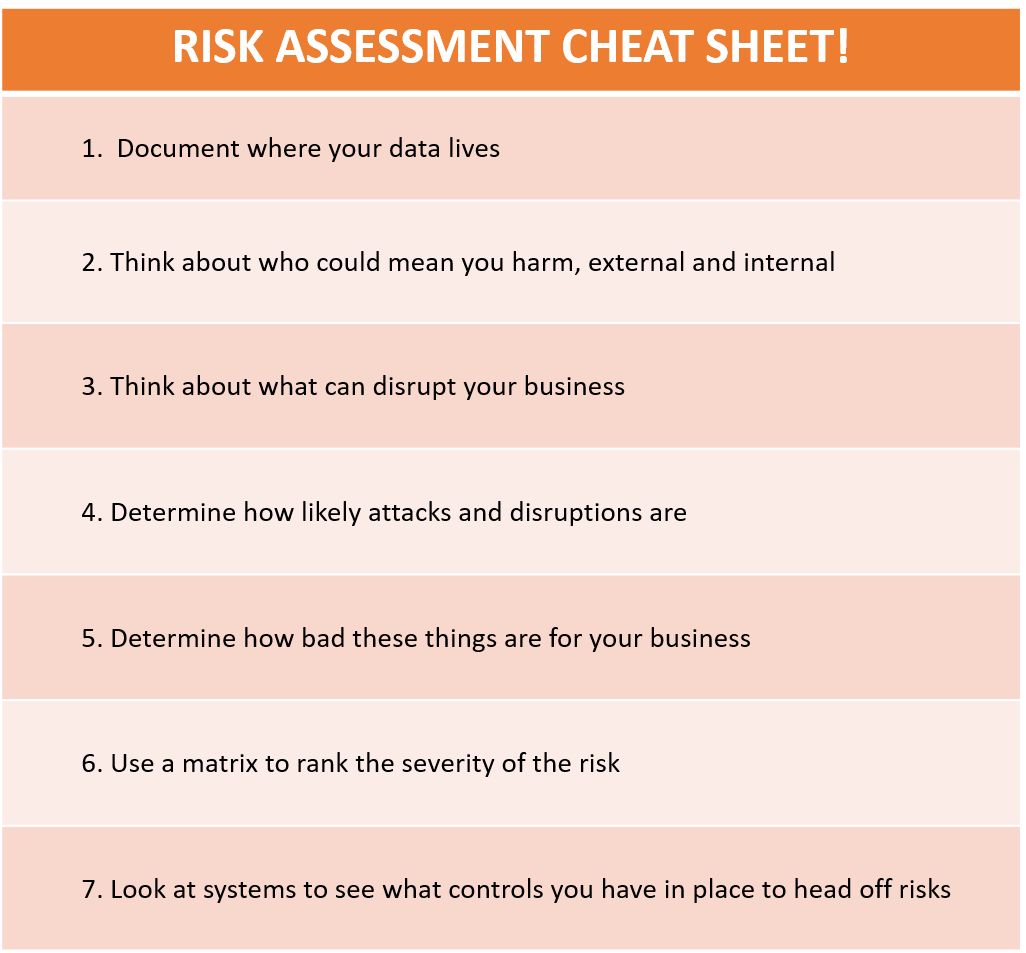
We've clipped an audio recording from our recent webinar "Gourmet Cyber Security on A Fast Food Budget" which explains each of those 7 checklist items from the cheat sheet in detail.
The webinar is intended for small to medium businesses who are looking for affordable ways to protect their organization, and includes information on how to:
- Conduct a basic security risk assessment
- Match IT security products to your level of risk
- Secure the best value for your investment
- And more...
We highly recommend that you watch the entire webinar but if you're short on time, just click on the recording below to learn the details behind the risk assessment cheat sheet - and don't forget to take notes!
Cybersecurity Risk Assessment Cheat Sheet
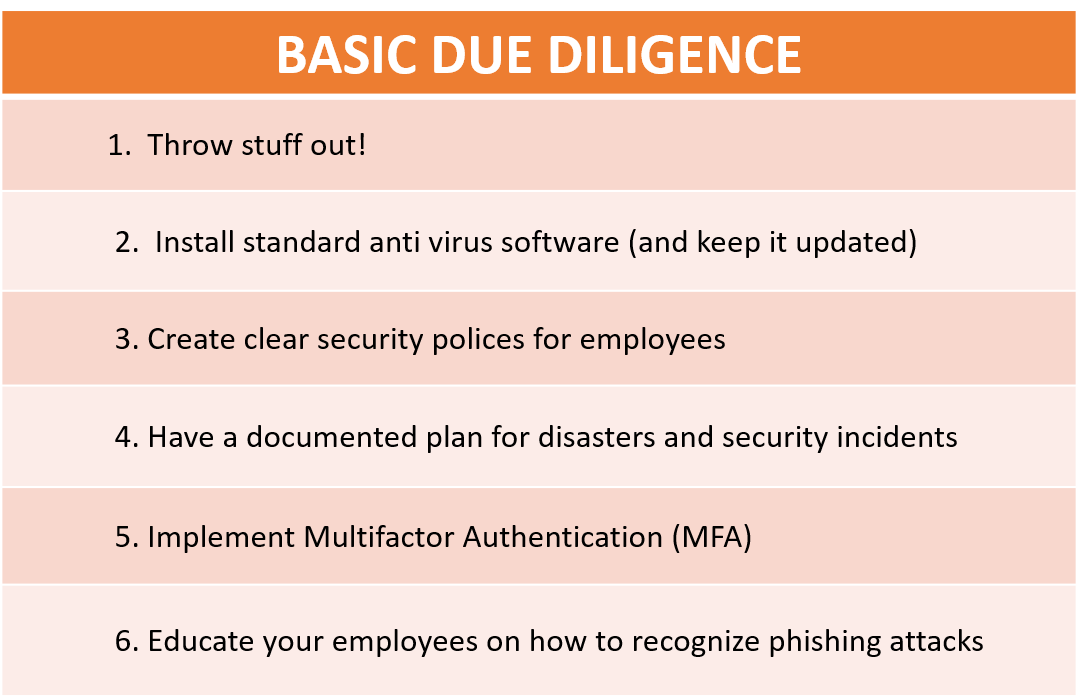
Step Four: Basic Due Diligence
Once you have determined your risk level, and determined where you think the most important areas are for you to invest in to reduce this risk, you need to do some basic due diligence.
These are the basic items that – god forbid – if you are ever on the witness stand somewhere, you will be able to say, “Well, of course our company does that!”
You can also find more details behind the items in the basic due diligence check list in the aforementioned webinar "Gourmet Cyber Security on A Fast Food Budget".
What Are Managed Cyber Security Services?
From a budget perspective, a lot has changed when it comes to cyber security solutions for smaller businesses.
As an example, Managed Security Services are one of the most cost-effective ways to get access to sophisticated security solutions, completely managed for you and billed on a monthly recurring basis.
Managed Security Services, also referred to as Security-as-a-Service, eliminate the need for large capital outlays, ongoing maintenance, and of course the need to recruit and maintain expensive cyber experts in-house.
Back to blog



.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)

