Microsoft Intune is a cloud-based service designed for mobile device management (MDM) and mobile application management (MAM).
Intune can be used to monitor and manage the security of any device that connects to the internet, whether it belongs to your company or it’s a personal device your employees are using for work.
That ability — to make sure you have control of how your company information is accessed, no matter what device people are using — is what makes Intune and integral part of your Microsoft 365 environment. Let’s take a closer look at how it works.
Don't want to read the article? Watch the full recording below.
Be sure to register here for the "Ntiva Live: Microsoft and You" webinar series!
What Is Intune and How Does It Work?
Intune supports digital security by allowing you to control how devices are used and configure policies to control the usage of your applications. It supports IOS, Android, Windows, and Macs, which makes it a versatile solution.
Adding to that versatility is that it can be used for both MDM and MAM:
- MDM is a management protocol for mobile devices, like tablets, and phones. It’s a key component of Microsoft Intune, and it gives you full control over your devices.
- By comparison, MAM is a lightweight option. It allows for control of corporate data and apps, but it doesn’t give up control of the entire device. That makes it the perfect option for personal devices your employees may use to access applications or sensitive data.
Intune operates from within the cloud and comes with a few key features, such as giving you the ability to manage devices and create individual profiles. It’s also enabled for data protection and to grant access to those applications in accordance with your device policy. Here’s an illustration of how these features interconnect:
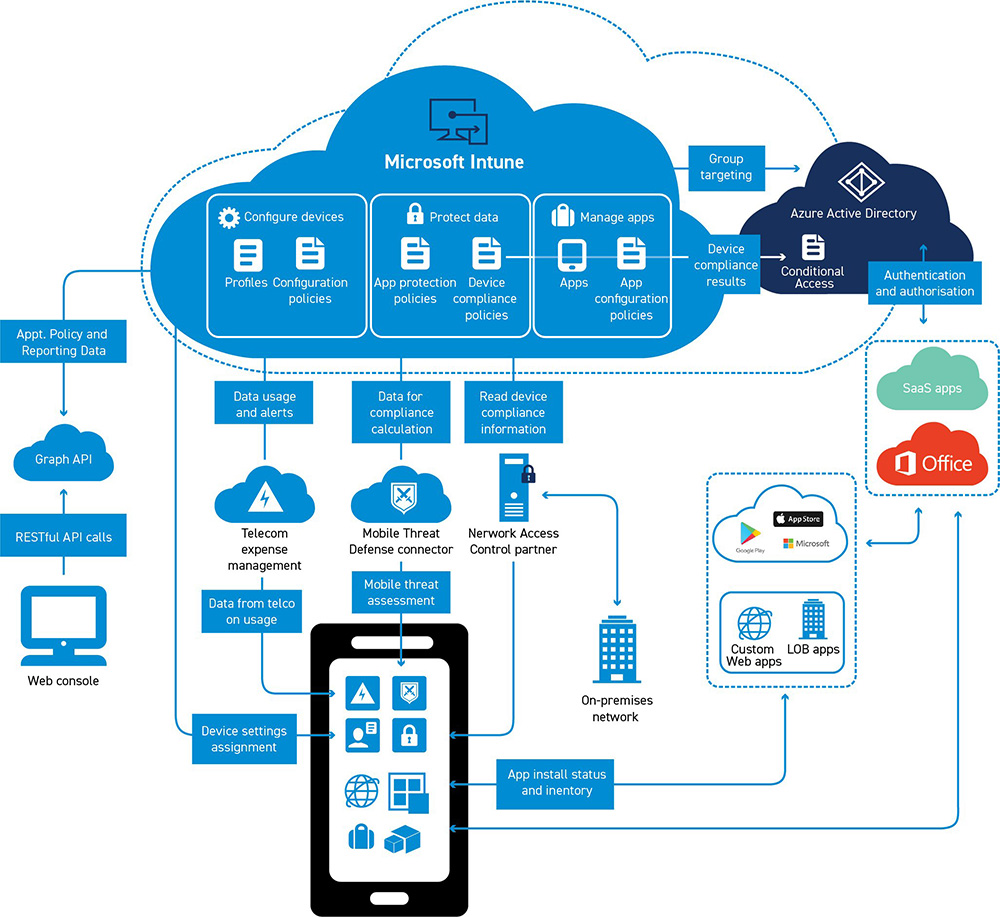
In this illustration, Intune is performing several operations to secure the device. Based on the configurations you set, you can determine the device policy to dictate what it’s able to do on your systems and what data it’s allowed to access. When new policies are released, Intune will automatically ensure the device adheres to those new standards — thus keeping your business protected.
What Happens When Devices Are Enrolled in Intune?
Once a device is enrolled in MDM, you can see it and all other devices that are accessing organization resources through your endpoint management dashboard. This allows you to look at how individual devices are behaving within the system.
For instance, this dashboard will show you which devices are configured properly and which ones are still non-compliant. You can also investigate a device to see which applications have been installed, define your policies, and identify which devices are compliant.
And speaking of compliance, another advantage of Intune is that it will automatically enroll a device into BitLocker, an encryption program that adds a significant layer of protection to your company’s information. Intune also maintains its own keys, which allows you to recover access if you lose a key or your device is no longer connected.
Intune’s MDM Provides Cybersecurity and Focused Control Over Enrolled Devices
Once a device is enrolled in Intune, you’ll have a wide range of options and tools to ensure that it’s working to the standards you set. That includes things like:
- Ability to see the devices enrolled and get an inventory of devices accessing organization resources
- Configuration of devices to meet your data security and health standards (for example, blocking jailbroken devices)
- Pushing certificates to devices so users can easily access your Wi-Fi network or use a VPN to connect to your network
- See reports to confirm users and device compliance
- Remove organization data if a device is lost, stolen, or not being used anymore
- The ability to wipe devices entirely if necessary
It’s worth noting here that we’re still talking about MDM. Many of these tools are great for use with corporate-owned machines, but not for someone’s personal device. For instance, while you might want to completely wipe a lost corporate device, you wouldn’t want to erase the contents of someone’s personal phone. Such devices should be enrolled in MAM instead.
Enrolling a Personal Device in Mobile Application Management
Earlier, we described MAM as Intune’s lightweight option, ideal for users accessing data from their personal devices. That’s because enrolling a device in MAM gives you the power to enable specific app protection, rather than the entire machine.
For example, if you have a user accessing a web version of Excel that contains sensitive data, you might want to control what they do with it. Intune allows you to put restrictions in place that prevent users from doing things like printing pages, taking screenshots, or downloading data. This allows you to protect company information while still granting users access from noncompany devices.
You can also use MAM to configure programs to perform certain functions. Say, for instance, you want to enable the auto-save function of an application someone is using. You can push that change through to the protected apps without affecting the rest of the device.
MAM is also helpful for gathering metrics. You can see reports on which apps are being used as well as tracking their usage. Finally, if you do need to remove data from someone’s device, you can perform a selective wipe that removes only your organization’s data from the apps in question.
Microsoft Intune and Windows Integrations
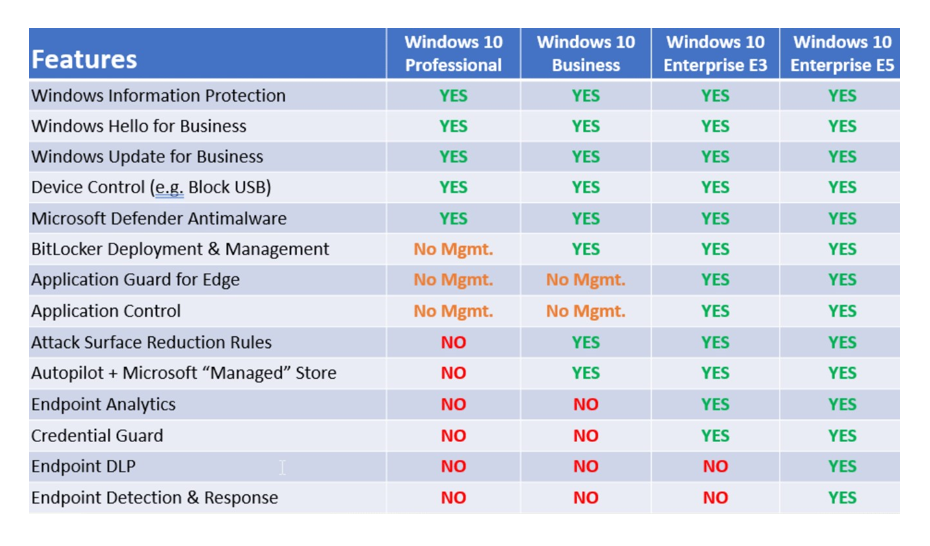
One important thing to note about Microsoft Intune is that some of its available features depend on what version of the Windows operating system your company uses. At a basic, Windows 10 Professional supports a small bundle of Intune functions but doesn’t manage features like BitLocker. On the other end of the spectrum, Windows 10 Enterprise E5 is configured to unlock the full suite of Intune capabilities, ensuring you have the highest level of security on those machines.Here's a complete breakdown of the Intune features available on each OS:
Enabling Intune to Interact With Conditional Access
If your company uses Microsoft’s cloud service Azure, whether that’s AD Premium 1 or AD Premium 2, you can set Intune to interact with conditional access.
To understand what that means, first let’s take a step back. Conditional access is a function of Microsoft Azure that makes sure your devices meet certain credentials or criteria. For example, if you require multi-factor authentication (MFA), your conditional access protocols would require your users to enroll in MFA as a condition of accessing your system.
Likewise, you can take the compliance profiles dictated by Intune and marry them with the conditional access protocols defined in Azure. This ensures that anyone not compliant with Intune’s requirements is unable to access your systems through Azure. That cooperation is a nice little touch from Microsoft that helps strengthen your overall security.
Microsoft Intune Protects Your Company's Sensitive Data
Intune is one of several Office 365 management tools that Microsoft offers to help your company protect you and your data. In an era when cybersecurity breaches of major corporations regularly appear in the headlines, it’s critical that you take steps to ensure you’re keeping information safe.
But as threats continue to evolve, and attackers become more sophisticated in their methods, it’s just as important that you stay up-to-date on the best practices for your organization. If you’d like to work with a partner as committed to cybersecurity as you are, we’d love to hear from you.
Back to blog



.png?width=420&height=280&name=Untitled%20design%20(10).png)

-1.jpeg?width=420&height=266&name=AdobeStock_1484542677%20(2)-1.jpeg)


